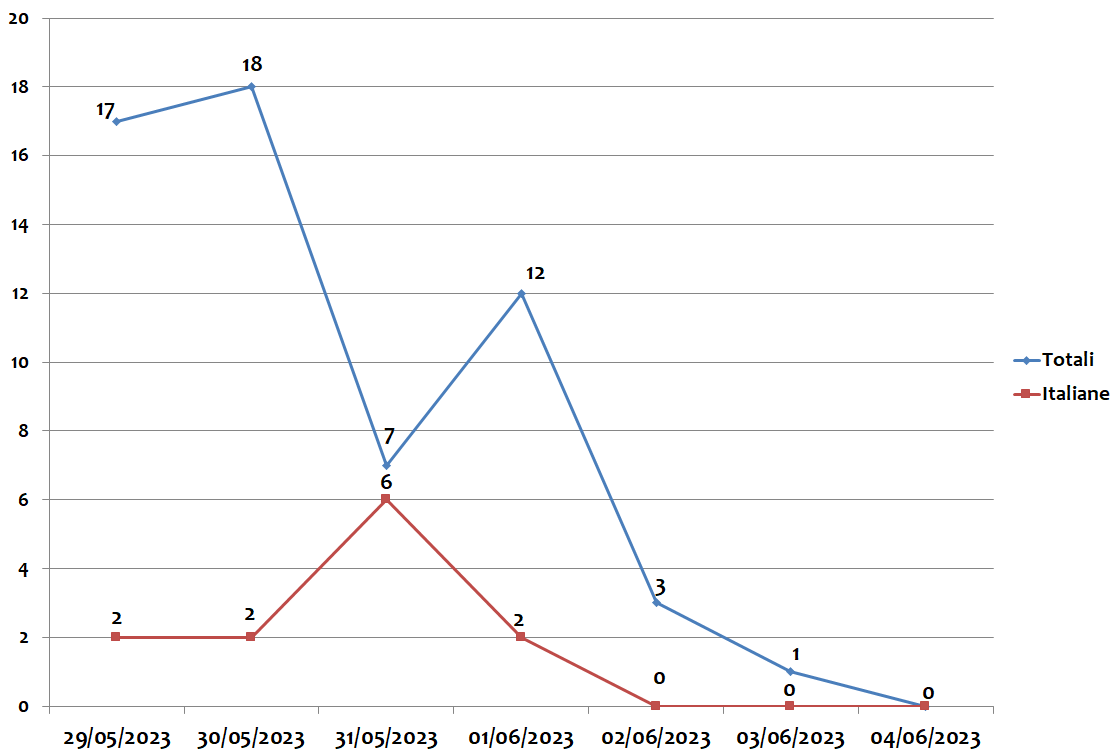
The Italian campaigns analyzed by TG Soft's C.R.A.M. were grouped according to macro categories, obtained from the subject of the email message used for malware distribution (malspam). Below we see the subjects used in the various campaigns divided by day and type of malware.
29/05/2023
FormBook - spread through a campaign themed "
Payments".
Remcos - spread through a campaign themed " "
Offers".
30/05/2023
AgentTesla - spread through a campaign themed "
Orders".
QakBot - spread through a campaign themed "
Various/reply-chain".
31/05/2023
AgentTesla - spread through two campaigns, the first themed "
Offers and the second themed "
Various".
FormBook - spread through a campaign themed "
Payments".
SnakeLogger - spread through a campaign themed "
Various".
QakBot - spread through a campaign themed "
Invoices".
Ursnif - spread through a campaign themed "
Invoices Corriere".
01/06/2023
QakBot - spread through a campaign themed "
Reservations".
Ursnif - spread through a campaign themed "
Invoices".
EMOTET
In the past week, the massive sending of MalSpam emails for the spread of the
Emotet malware, was not detected.
Find out if you are an Emotet target!
TG Soft, as reported in the information "
HAVEiBeenEMOTET portal to find out whether a mailbox has been used in malspam campaigns to spread EMOTET "has provided and maintained for over a year the
HAVEiBeenEMOTET service, which is useful to check if your email addresses or domains are targeted by Emotet.
With this service you can check for free if your email addresses/domains are involved or are targets of MalSpam by Emotet
.
Advanced search features and the IOC feed are available by registering and activating the API service at the link:
HAVEiBeenEMOTET - API