|
TG Soft's C.R.A.M. (Anti-Malware Research Center) analyzed an email included in a campaign spreading the malware Trojan Ursnif sent on May 17, 2019.
Cyber-criminals developed "Social engineering" methods for fraudulent mass mailings, to induce the victim to open infected attachments or click on links in the body of the message.
|
INDEX
|
Fake Invoice Email Spreads Ursnif Trojan
Description:
The
malspam sending campaign was detected in the morning of May 17, 2019.
The emails are presented with a short variable message that prompts the opening of the link contained in the email.
We report an email example:
|
Subject: [Amministrazione] Fattura N. 244 del 29/04/2019
|
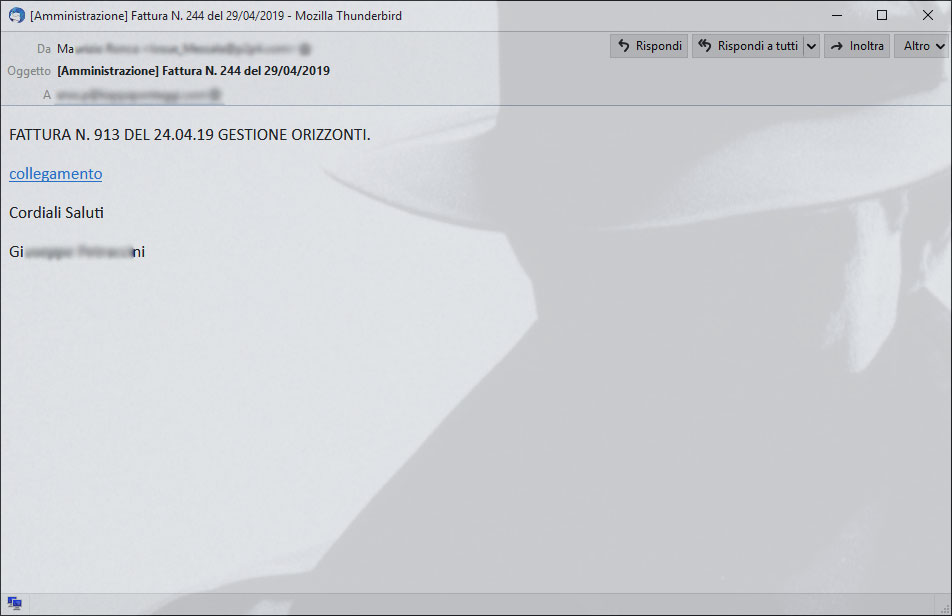 |
| [Amministrazione] Fattura N. 244 del 29/04/2019 - Mozilla Thunderbird |
Da:
Oggetto: [Amministrazione] Fattura N. 244 del 29/04/2019
A: |
FATTURA N. 913 DEL 24.04.19 GESTIONE ORIZZONTI.
collegamento
Cordiali Saluti
Gi ini
|
| |
|
| |
Other examined emails hide the malicious link with these other wordings:
- download here
- your link
- here
When you open the site linked in the email (
http://lucabrasisitaliandelinyc[.]com/dTrHewDju?lqGmPcjP=61288), a ZIP archive file is downloaded with the name "
Nuovo ducumento 1.zip" :
- File Name: Nuovo ducumento 1.zip
- Size: 219624 Byte
- Md5: DFFD2F439E7FBFA1FE9A5FCD757450B3
Inside the
ZIP is a
VBS file and a fake image (see below) to fool the user. The examined Dropper has the following characteristics.:
- File Name: Nuovo documento 1.vbs
- Size: 164748 Byte
- Md5: CF836263499F015F00D9D2FEC5E632EF
- Malware family: Dropper
- VirIT: Trojan.VBS.Dropper.CK
|
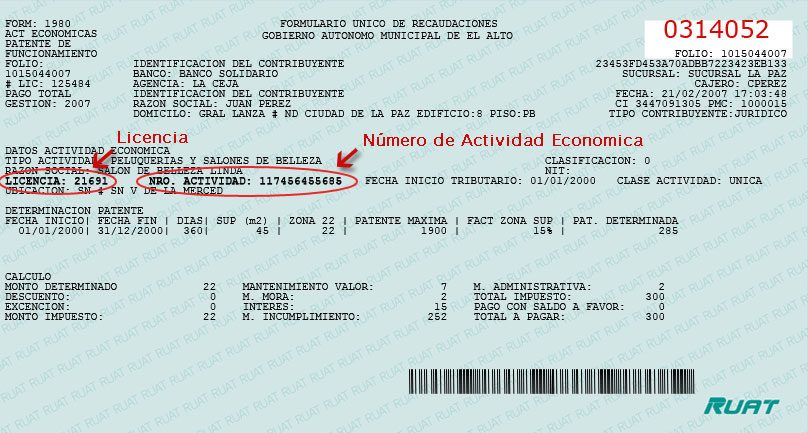
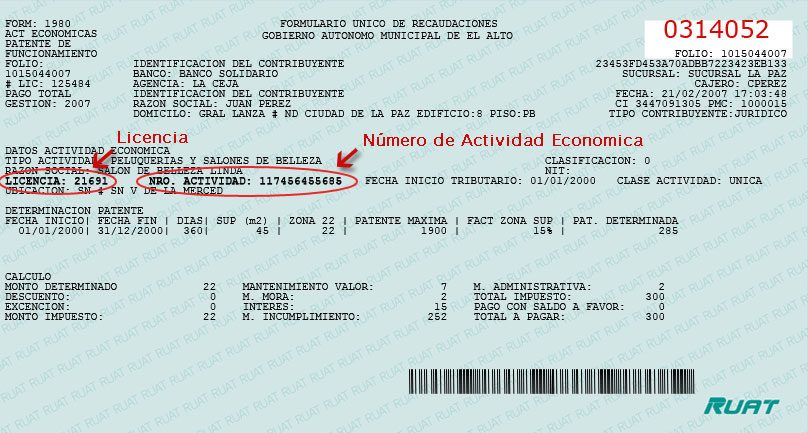
img. fake
|
When you open the VBS file (
Nuovo documento 1.vbs) a link will be made to the
http://gaetanascucinaitaliananyc[.]com/pagiy75.php that will download the payload of the Ursnif malware which will be saved in the %temp% folder with the name "VideoBoost.exe" and then run.
The Ursnif malware sample examined is:
- File Name: VideoBoost.exe
- Dimension: 522912 Byte
- Md5: 0B5FF24EF39C68F6C2948A65E014ADBA
- Malware family: Ursnif
- VirIT: Trojan.Win32.Ursnif.KL
- Digital signature: WIKI SKIN LIMITED
- Compilation Date: 2018-05-15 14:45:28
The examined Ursnif malware then connects to the
Command and Control (C&C) Server at the address
http://kolqvbanle[.]com/index.htm
More details about the Ursnif malware can be viewed at the following links:
IOC
MD5:
DFFD2F439E7FBFA1FE9A5FCD757450B3 [ZIP]
CF836263499F015F00D9D2FEC5E632EF [VBS]
0B5FF24EF39C68F6C2948A65E014ADBA [URSNIF]
URL:
http://lucabrasisitaliandelinyc[.]com/dTrHewDju?lqGmPcjP=61288 -> OLD IP: 212.109.194.253 NEW IP:212.109.195.28 - ASN: AS29182 JSC The First
http://lavillacafebk[.]com/QFGba?BbWJC=54
http://littleluigipizzact[.]com/fQQxhYFSH?kFo=174
http://manganarosheroboynyc[.]com/hlqhlyZC?Skcu=6345
http://order42ndstpizzacorp[.]com/Iprr?XQc=54
http://midwestgrillcambridge[.]com/RgEX?uxRcoV=846216
http://mexicanpostlovepark[.]com/BJjVynHr?VvCK=51
http://gaetanascucinaitaliananyc[.]com/pagiy75.php -> IP: 79.174.12.253 - ASN: AS29182 JSC The First
https://kolqvbanle[.]com/index.htm -> IP: 46.17.45.187 - ASN: AS51659 LLC Baxet
Back to top of page
How to identify a fake email
Experience and common sense are the first weapons to avoid these kinds of scams.
Careful reading of the email, in all its elements, is essential. Be wary of
ZIP-formatted attachments and, if possible, DO NOT enable automatic
macro execution. It is strongly discouraged to set up automatic execution of macros since simply opening
Word and
Excel files will see the immediate execution of macros without any prior alert.
In case you have been infected by a
Banker, the advice from TG Soft's C.R.A.M. is to take appropriate security precautions
even after the remediation of the system(s) involved, such as changing the most commonly used passwords on the Web. In case the workstation involved is used for home-banking transactions, an assessment with your
credit institution is also recommended.
How to send suspicious emails for analysis as possible virus/malware/ransomware and/or Phishing attempts
Sending materials to the TG Soft's Anti-Malware Research Center for analysis, which is always free of charge, can be done safely in two ways:
- Any suspect email can be sent directly by the recipient's e-mail, to the following mail lite@virit.com,choosing as sending mode "Forward as Attachment" and inserting in the subject section "Possible phishing page to verify" rather than "Possible Malware to verify";
- Save the e-mail to be sent to TG Soft's C.R.A.M. for analysis as an external file to the e-mail program used. The resulting file must be sent by uploading it from the page Send Suspicious Files (http://www.tgsoft.it/italy/file_sospetti.asp). Obviously if you want a feedback on the analysis of the data submitted, you have to indicate an e-mail address and a brief description of the reason for the submission (for example: possiible / probable phishing; possible / probable malware or other).
We give you these suggestions to help avoiding credential theft, viruses/malware or even worse next-generation Ransomware / Crypto-Malware.
Integrate your PC / SERVER protection with Vir.IT eXplorer Lite
If you are not yet using Vir.IT eXplorer PRO, it is advisable to install, Vir.IT eXplorer Lite -FREE Edition-.to supplement the antivirus in use to increase the security of your computers, PC and SERVER indifferently,
Vir.IT eXplorer Lite has the following special features: |
 |
- freely usable in both private and corporate environments with Engine+Signature updates without time limitation;
- Interoperable with any other AntiVirus, AntiSpyware, AntiMalware or Internet Security already present on PCs and SERVERs. We recommend to use it as a supplement to the AntiVirus already in use as it does not conflict or slow down the system but allows to significantly increase security in terms of identification and remediation of infected files;
- It identifies and, in many cases, even removes most of the viruses/malware actually circulating or, alternatively, allows them to be sent to the C.R.A.M. Anti-Malware Research Center for further analysis to update Vir.It eXplorer PRO;
- Through the Intrusion Detection technology, also made available in the Lite version of Vir.IT eXplorer, the software is able to report any new-generation viruses/malware that have set in automatically and proceed to send the reported files to TG Soft's C.R.A.M.
- Proceed to download Vir.IT eXplorer Lite from the official distribution page of TG Soft's website.
For Vir.IT eXplorer PRO users...
 |
For Vir.IT eXplorer PRO owners, it is also possible to contact for free TG Soft's technical phone support.The details can be found on the support page CLIENTS. |
C.R.A.M.
TG Soft's Anti-Malware Research Center
Back to top of page