PHISHING INDEX
Below are the most common email phishing attempts detected by the TG Soft Anti-Malware Research Center in
February 2026:
25/02/2026 =>
ING Bank
24/02/2026 =>
PayPal
23/02/2026 =>
Aruba - Pending messages
22/02/2026 =>
SumUp
20/02/2026 =>
WeTransfer
19/02/2026 =>
Aruba - Support request
19/02/2026 =>
OneDrive
18/02/2026 =>
Bank
18/02/2026 =>
Tiscali
12/02/2026 =>
SumUp
03/02/2026 =>
Webmail
These emails aim to deceive unsuspecting victims into providing sensitive information, such as bank account details, credit card codes, or personal login credentials, with all the easily imaginable consequences.
25 February 2026 ==> Phishing ING Bank
SUBJECT: <
ING service: a one-time confirmation of your data is required>
We have identified another phishing attempt pretending to be an official communication from
ING.
The message warns the unsuspecting recipient: ‘
In accordance with the new EU directives on payment service security (PSD2) and in order to improve the protection of your data in online banking, a one-time confirmation of your account details is required.’ The recipient must confirm his/her details by
28 February to avoid a temporary restriction of the account. He/she is then invited to complete the procedure via the following link:
Register now securely
ING is clearly not involved in the mass sending of these emails, which are scams whose aim, as always, is to steal the home banking login credentials of unsuspecting recipients.
Looking at the message, we can see straight away that it's pretty generic and that the sender's email address <
noreply(at)baaaaaaaadr(dot)firebaseapp(dot)com> isn't linked to the
ING official domain. Another unusual aspect is the request to update personal data by entering online banking credentials through a link sent via email.
The link in the message redirects us to a web page that is supposed to simulate the official
ING website but it actually redirects to a page already reported as a DECEPTIVE PAGE/WEBSITE. In fact it is actually managed by cybercriminals whose goal is to obtain your most valuable data so that they can use it for their own purposes.
To conclude, we urge you to always be wary of any email that asks you to enter confidential information, and avoid clicking on suspicious links, which could lead to a fake website difficult to distinguish from the original one.
24 February 2026 ==> Phishing PayPal
SUBJECT: <
Your Account Security: Unrecognized Login from [Santorini, Grecia]>
Below, we analyse a new phishing attempt that aims to steal login credentials for
PayPal accounts, the well-known US digital payments company.
The message informs the recipient that access to his/her
PayPal account has been detected from a unrecgnised device, and also provides details of the device that accessed the account, its location, date and time. It then warns him/her that if he/she did not perform the operation, it is necessary to follow the security procedure indicated below to protect the account and the account holder's personal data. The user can verify the reported suspicious activity by using the link:
Secure your account
When we look at the message, we see that it has an email address <
lina[at]elettro3s[dot]it> that clearly isn't linked to the official
PayPal domain. This is definitely weird and should make us suspicious
Anyone who unluckily clicks on the
Secure your account link, will be redirected to a web page unrelated to
PayPall, but designed to obtain your most valuable data for criminal purposes.
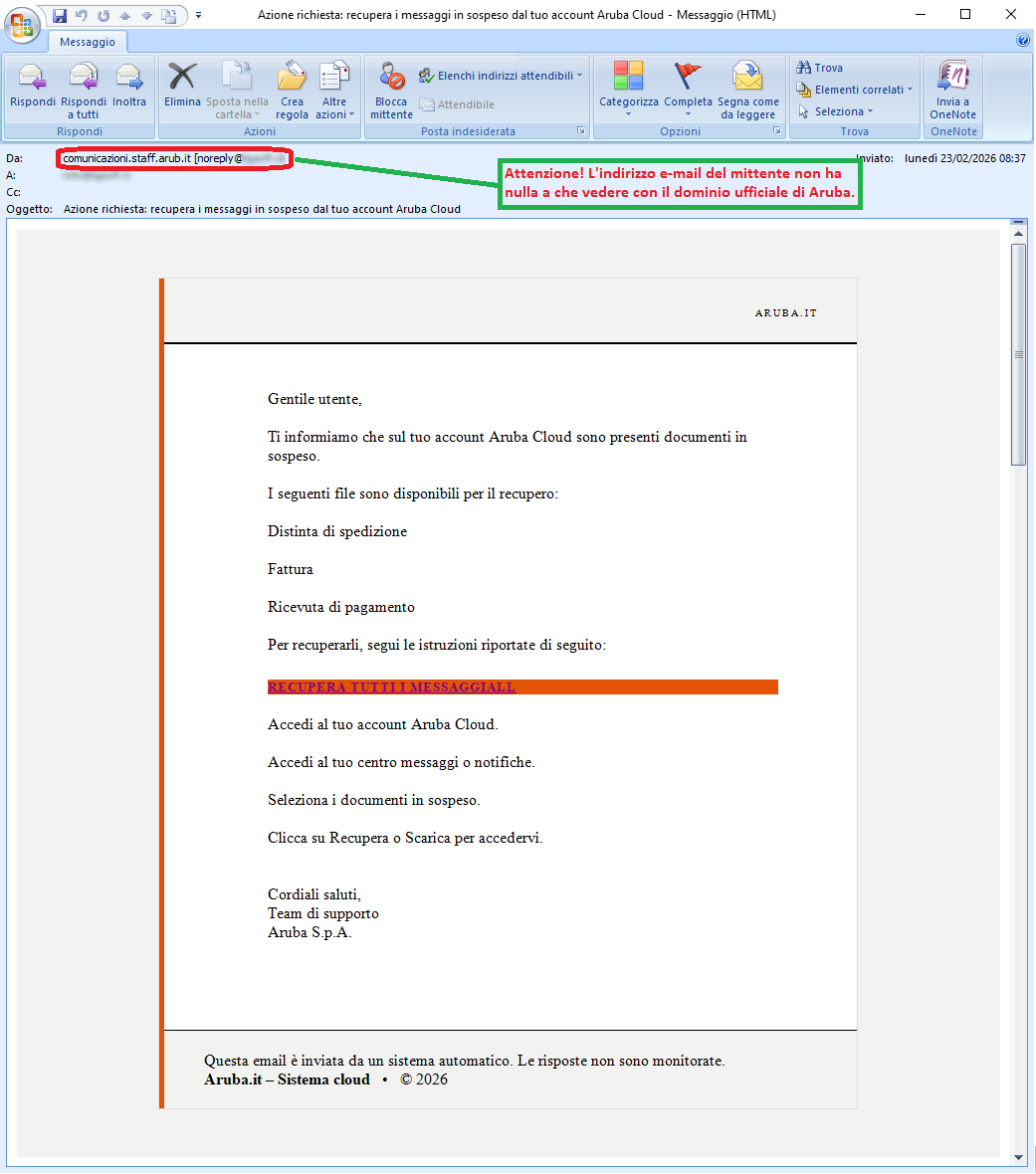
23 February 2026 ==> Phishing Aruba - Pending messages
SUBJECT: <
Action required: retrieve pending messages from your Aruba Cloud account>
Below is another phishing attempt pretending to be a communication from the
Aruba brand.
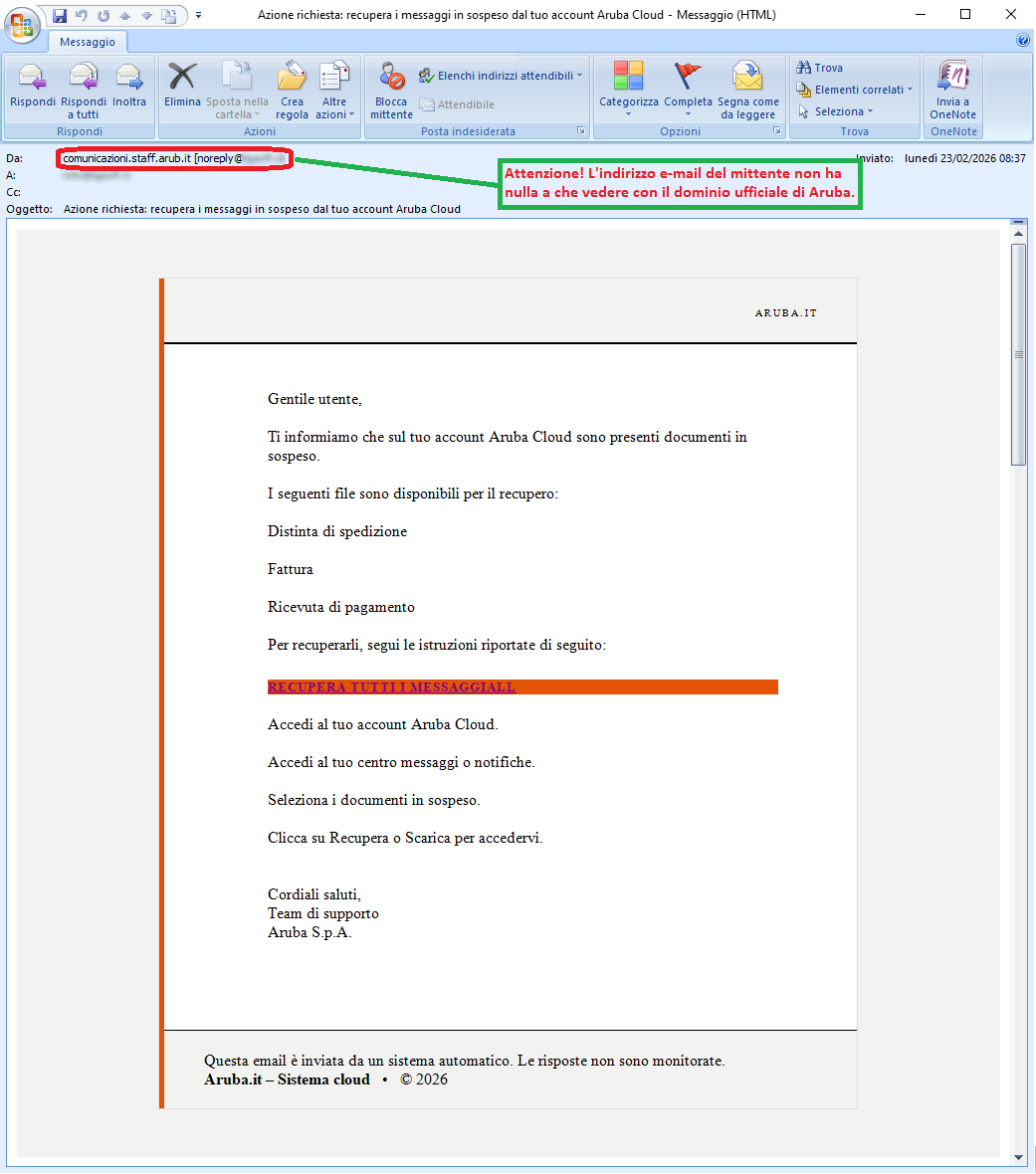
This time, the message informs the recipient that there are pending documents in his/her account.
The files available for recovery are then listed, but they are very generic:
"
Delivery note
Invoice
Payment receipt"
It then warns him/her that in order to recover the files, he/she must follow the instructions provided via the following link:
RECOVER ALL MESSAGESALL
The well-known web hosting, e-mail and domain registration company
Aruba is clearly not involved in the mass sending of these emails, which are genuine scams whose aim, as always, is to steal sensitive data from unsuspecting recipients.
When we carefully examine the message, there are some clues that should raise suspicion. We immediately see that the email address of the message <
noreply[at]****l>, does not belong to the official
Aruba domain. This is definitely unusual and should make us suspicious
Anyone who unluckily clicks on the link will be redirected to a fraudulent web page, which has already been reported as a DECEPTIVE SITE because it is managed by cybercriminals whose goal is to obtain your most valuable data in order to use it for their own purposes.
We always urge you to pay attention to every detail, even trivial ones, not to rush and not to enter your personal details and/or passwords on forms hosted on counterfeit web pages.
22 February 2026 ==> Phishing SumUp
SUBJECT: <
Alerta de Seguridad: Actualización Obligatoria 2026>
Below, we analyse another phishing attempt that pretends to be an official communication from
SumUp, a well-known London-based digital payments company.
The message, this time in Spanish, notifies the recipient of a report concerning the security of the user's account and warns: ‘
Our system has detected an irregularity in the security parameters that makes it essential to immediately apply Protection Patch 2026. This update is essential to neutralise potential intrusion risks and preserve the confidentiality of your information.’
It also warns him/her that, if he/she does not update his details via the link provided, his/her account will be temporarily blocked for security reasons:
INICIAR VERIFICACION AHORA
The well-known London-based company is clearly not involved in the mass sending of these emails, which are genuine scams whose aim, as always, is to steal sensitive data from unsuspecting recipients.
A careful analysis of the message reveals some clues that should raise suspicion. We immediately notice that the email address of the message <
noreply-pci2p7[at]teamdizza-a9056[dot]firebaseapp[dot]com> does not belong to the official
SumUp domain. This is highly unusual and should make us very suspicious. Another strange fact is that the email does not provide any customer identification details and asks you to enter your account credentials via a link sent by email.
Anyone who unfortunately clicks on the
INICIAR VERIFICACION AHORA link, will be redirected to a malicious web page, which has already been reported as a DECEPTIVE PAGE/WEBSITE, as it is managed by cybercriminals whose aim is to obtain your most valuable data so that they can use it for their own purposes.
20 February 2025 ==> Phishing WeTransfer
SUBJECT: <
postacert@comune.gov.it has sent you 3 files via WeTransfer>
Below, we analyse a phishing attempt that aims to steal
WeTransfer account credentials
The message informs the recipient that he/she has received 3 files and invites him/her to log in to download the files via the following link:
Download files
When we examine the email, we immediately notice an inconsistency in the information. In fact, while the subject line indicates that the sender of the files is <
postacert(at)comune(dot)gov(dot)it>, the message has an email address that cannot be traced back to the sender indicated in the body of the message, nor to
WeTransfer <info(at)ilbivio-hotel(dot)it>. This is definitely unusual and should make us suspicious.
Anyone who unfortunately clicks on the
Download files link, will be redirected to a malicious web page, which has already been reported as a DECEPTIVE SITE. In fact, it is managed by cybercriminals whose goal is to get hold of your most valuable data so that they can use it for their own purposes.
19 February 2026 ==> Phishing Aruba - Support request
SUBJECT: <
Aruba.it – Support request no. [17014283M]>
This month, we once again encounter phishing attempts pretending to be communications from the
Aruba brand
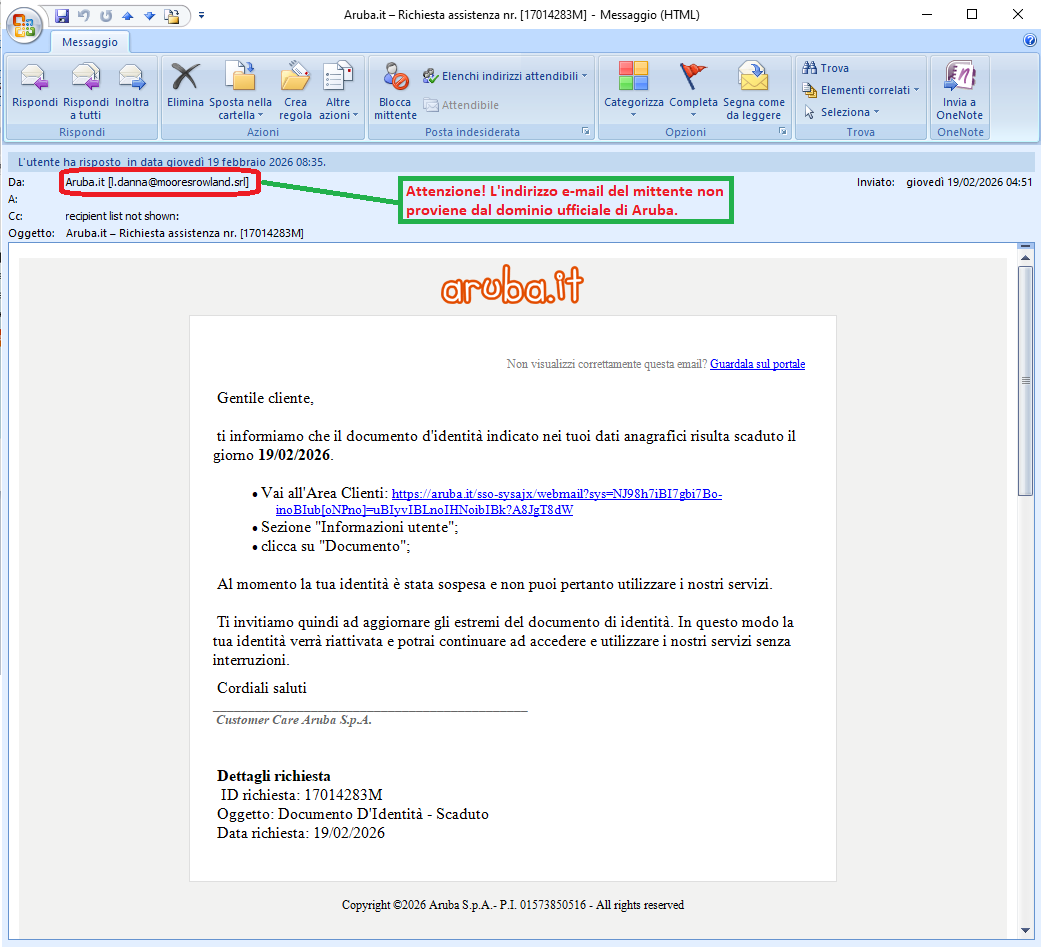
. This time, the message informs the recipient that the identity document indicated in his/her personal data expired on
19/02/2026.
It therefore warns him/her that his/her identity has been suspended and he/she cannot use the services at this time. To reactivate the account, he/she must update his/her personal details by logging into the Customer Area and clicking on “
User Information” and “
Document”.
It then invites the user to proceed via the following link:
https[:]//aruba[.]it/sso-sysajx/webmail?sys=NJ98h7iBI7gbi7Bo-inoBIub[oNPno]=uBIyvIBLnoIHNoibIBk?A8JgT8dW
The well-known web hosting, e-mail and domain registration company
Aruba is clearly not involved in the mass sending of these emails, which are genuine scams whose aim, as always, is to steal sensitive data from unsuspecting recipients.
When we examine the message carefully, there are some clues that should raise suspicion. We immediately notice that its the email address <
l(dot)danna[at]mooresrowland[dot]srl> does not belong to the official
Aruba domain, an anomaly that should make us suspicious.
Anyone who unfortunately clicks on the link will be redirected to a web page that, although it graphically simulates the
Aruba account login page – due to the presence of the well-known company's logo – has an unusual address/domain:
https[:]//FakeDomainName*]
On this page, users are invited to access his/her customer area by entering his/her email login and password to update his/her personal details and reactivate services.
We always urge you to pay attention to every detail, even trivial ones, not to rush and not to enter your personal details and/or passwords on forms hosted on fake web pages, as these will be sent to the cybercriminals behind the scam, who will use them for illegal purposes.
19 February 2026 ==> Phishing OneDrive
SUBJECT: <
New work order approved by “Company Name PLC”>
Below, we analyse a phishing attempt that aims to steal
OneDrive account credentials.
The message informs the recipient that he/she has received a file named
Dichiarazione.pdf (Statement.pdf) on
OneDrive from a PLC company. It then invites him/her to view the attached document by clicking on the following link:
NomeSocietà S.p.A. - Dichiarazione.PDF (Companyname PLC-Statement.PDF)
When we examine the message, we see an email address seemingly originating from the domain of the mentioned company.
However, when we open the attachment, we notice some suspicious elements.
When we click on the link, we are redirected to a web page that asks the user to log in again to view the two PDF files received online.
Actually, the page where we're redirected to enter our
OneDrive credentials is hosted on a suspicious address/domain, which we've listed below:
https[:]//[FakeDomainName*]
We urge you to always pay attention to every detail, even trivial ones, and not to enter your personal details and/or passwords on forms hosted on counterfeit web pages, as they will be sent to a remote server and used by cyber fraudsters, with all the associated risks that this entails.
18 February 2026 ==> Phishing Bank
SUBJECT: <
Confidential Notice: Confirmation of Information Associated with Your Profile>
We find again this month the phishing campaign that spreads through an e-mail exploiting stolen graphics or similar to the graphics of a well known bank. Hence it tries to pass itself off as an official communication, in order to induce the unsuspecting recipient to do what requested, and fall into a social engineering trap.
The message informs the unsuspecting recipient that, for security reasons, his/her profile information, particularly his/her contact details, must be confirmed in order to ensure that his/her account is fully operational.
To confirm, we just need to click on the link:
CONFIRM DATA
We can immediately see that the message comes from a highly suspicious email address <
millo(at)ceripe(dot)it> and contains very generic text, despite the fact that the cybercriminal has included the bank's logo in order to mislead the user. The intention is to trick the victim into logging into his or her banking app so that the data can be stolen.
The purpose is to get the recipient to click on the
CONFIRM DATA link, which, we must point out, redirects to a page that has already been reported as a DECEPTIVE WEBSITE. In fact, it is managed by cybercriminals whose goal is to obtain your most valuable data in order to use it for criminal purposes.
18 February 2026 ==> Phishing Tiscali
SUBJECT: <
(Urgent deactivation notice)>
Below we analyse a phishing attempt that aims to steal
TISCALI account login credentials.
The message informs the recipient that his/her email has expired and has been deactivated, meaning that it is no longer possible to send or receive messages until it is reactivated. The email warns the user that, one day after the expiry date, all messages will be deleted.
The user is then asked to reactivate his/her account as soon as possible via the following link:
REACTIVATE NOW
Looking closely at the message, there are some clues that should raise suspicion. We immediately notice that its email address <
milantns[at]sbb[dot].rs> does not belong to the official
TISCALI domain, a definite red flag. Another warning sign is that, in order to confirm, the user is asked to enter his/her account credentials via a link provided in the email
Anyone who unfortunately clicks on the
REACTIVATE NOW link, will be redirected to a web page which, although it graphically simulates the
TISCALI account login page by including the company logo, is not at all trustworthy. In this case too, the address is abnormal:
https[:]//FakeDomainName*]
On this page, users are invited to log in to his/her customer area, where he/she can then reactivate his/her account to avoid losing data.
We always urge you to pay attention to every detail, even trivial ones, not to rush and not to enter your personal details and/or passwords on forms hosted on fake web pages, as these will be sent to the cybercriminals behind the scam, who will use them for illegal purposes.
12 February 2026 ==> Phishing SumUp
SUBJECT: <
Final notice: account verification required - Code: 761427>
Below, we analyse a new phishing attempt that pretends to be an official communication from
SumUp, a well-known London-based digital payments company.
The message, which concerns the security of the user's account, warns:
‘We have detected unusual activity on your account. For your security, access has been temporarily restricted. Please verify your information to restore full access.’
To verify, simply click on the following link:
Verify Account
The well-known London-based company is clearly not involved in the mass sending of these emails, which are genuine scams whose aim, as always, is to steal sensitive data from unsuspecting recipients.
A careful analysis of the message reveals some clues that should raise suspicion. We immediately notice that the email address of the message <
mail[at]dcaef0dc22[dot]nxcli[dot]io> does not belong to the official
SumUp domain. This is highly unusual and should definitely raise suspicion. Another strange fact is that the email does not provide any customer identification details and asks him/her to enter his/her account credentials via a link provided in the email.
Anyone who unluckily clicks on the
Verify Account link, will be redirected to a web page which, although it graphically simulates the
SumUp account login page due to the presence of the well-known company's logo, has an unusual address/domain:
https[:]//[FakeDomainName*]
On this page, users are invited to access their customer area by entering their email login and password and then proceed with the requested update.
We therefore urge you to always pay close attention to even the smallest details and not to enter your personal details and/or passwords on forms hosted on counterfeit web pages, as they will be used by cyber fraudsters for illegal purposes.
03 February 2026 ==> Phishing Webmail
SUBJECT: <
Undelivered messages report>
Below, we analyse the phishing attempt that aims to steal the email account credentials of the victim.
The message, in English, informs the recipient that his/her email account password will expire today and that he/she must update it as soon as possible in order to continue using the services linked to it. To keep the password, he/she use the following link:
Use Same Sign In Credentials
When we examine the message, we see that it has an email address <
cs(at)eita(dot)co(dot)id> that seems to belong to the recipient's email domain. This is highly unusual and should make us very suspicious.
Anyone who unfortunately clicks on the
Use Same Sign In Credentials link, will be redirected to a fraudulent web page, which is designed to imitate the email account login page.
On this page, the user is invited to log in to his/her account by entering, in particular, the password for his/her e-mail account to confirm or change his/her current password, which is supposed to expire.
Actually, the page where the user is redirected to enter his or her email account credentials is hosted on an anomalous address/domain, which we report below:
https[:]//[FakeDomainName*]
We urge you to always pay attention to every detail, even trivial ones, and not to enter your personal details and/or passwords on forms hosted on counterfeit web pages, as they will be sent to a remote server and used by cyber fraudsters, with all the associated risks that this entails.
A little attention and a quick glance can save you a lot of hassle and headaches...
We urge you NOT to be fooled by these types of e-mails, which, even though they use familiar and not particularly sophisticated approach techniques, if there is a resurgence, with reasonable likelihood more than a few unfortunates will be fooled.
We invite you to check the following information on phishing techniques for more details:
04/12/2025 15:56
- Phishing: the most common credential and/or data theft attempts in December 2025...
04/11/2025 14:45
- Phishing: the most common credential and/or data theft attempts in Novembre 2025...
01/10/2025 16:40 - Phishing: the most common credential and/or data theft attempts in October 2025...
04/09/2025 09:45 - Phishing: the most common credential and/or data theft attempts in September 2025...
05/08/2025 08:58- Phishing: the most common credential and/or data theft attempts in August 2025...
01/07/2025 16:04 - Phishing: the most common credential and/or data theft attempts in July 2025.
05/06/2025 09:22 - Phishing: the most common credential and/or data theft attempts in June 2025...
05/05/2025 15:03 - Phishing: the most common credential and/or data theft attempts in May 2025...
07/04/2025 14:22 - Phishing: the most common credential and/or data theft attempts in April 2025...
07/03/2025 15:10 - Phishing: the most common credential and/or data theft attempts in March 2025..
03/02/202514:54 - Phishing: the most common credential and/or data theft attempts in February 2025...
03/01/2025 14:40 - Phishing: the most common credential and/or data theft attempts in January 2025...
Try Vir.IT eXplorer Lite
 If you are not yet using Vir.IT eXplorer PRO, it is advisable to install Vir.IT eXplorer Lite -FREE Edition- to supplement the antivirus in use to increase the security of your computers, PCs and SERVERS.
If you are not yet using Vir.IT eXplorer PRO, it is advisable to install Vir.IT eXplorer Lite -FREE Edition- to supplement the antivirus in use to increase the security of your computers, PCs and SERVERS.
Vir.IT eXplorer Lite has the following special features:
- freely usable in both private and corporate environments with Engine+Signature updates without time limitation;
- fully interoperable with other AntiVirus software and/or Internet Security products (both free and commercial) already installed on your computer. It doesn't need any uninstallation and it doesn't cause slowdowns, as some features have been appropriately reduced to ensure interoperability with the AntiVirus software already on your PC/Server. This, however, allows cross-checking through the scan;
- it identifies and, in many cases, even removes most of the viruses/malware actually circulating or, alternatively, allows them to be sent to the C.R.A.M. Anti-Malware Research Center for further analysis to update Vir.It eXplorer PRO;
- through Intrusion Detection technology, also made available in the Lite version of Vir.IT eXplorer, the software is able to report any new-generation viruses/malware that have set in automatically and send the reported files to TG Soft's C.R.A.M
- Download Vir.IT eXplorer Lite from the official distribution page of TG Soft's website.
VirIT Mobile Security AntiMalware ITALIAN for ALL AndroidTM Devices
VirIT Mobile Security Italian Anti-Malware software that protects Android™ smartphones and tablets, from Malware intrusions and other unwanted threats, and empowers the user to safeguard his/her privacy with an advanced heuristic approach (Permission Analyzer).

TG Soft makes VirIT Mobile Security available for free by accessing the Google Play Store market (https://play.google.com/store/apps/details?id=it.tgsoft.virit) from which you can download the Lite version, which can be freely used in both private and corporate settings.
You can upgrade to the PRO version by purchasing it directly from our website=> click here to order
Acknowledgements
TG Soft's Anti-Malware Research Center would like to thank all users, customers, reseller technicians, and all people who have transmitted/reported material attributable to Phishing activities to our Research Center, that allowed us to make this information as complete as possible.
How to submit suspicious emails for analysis as possible phishing but also virus/malware or Crypto-Malware
You can submit materials to TG Soft's Anti-Malware Research Center safely and free of charge in two ways:
- any suspect email can be sent directly by the recipient's e-mail, to the following mail lite@virit.com,choosing as sending mode "Forward as Attachment" and inserting in the subject section "Possible phishing page to verify" rather than "Possible Malware to verify";
- save the e-mail to be sent to TG Soft's C.R.A.M. for analysis as an external file to the e-mail program used. The resulting file must be sent by uploading it from the page Send Suspicious Files (http://www.tgsoft.it/italy/file_sospetti.asp). Obviously if you want a feedback on the analysis of the data submitted, you have to indicate an e-mail address and a brief description of the reason for the submission (for example: possiible / probable phishing; possible / probable malware or other).

For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page:
How to send suspicious emails for analysis
We provide all this information to help you prevent credential theft, viruses/malware or, even worse, next-generation Ransomware / Crypto-Malware.
TG Soft Anti-Malware Research Centre (C.R.A.M.)


 This time, the message informs the recipient that there are pending documents in his/her account.
This time, the message informs the recipient that there are pending documents in his/her account.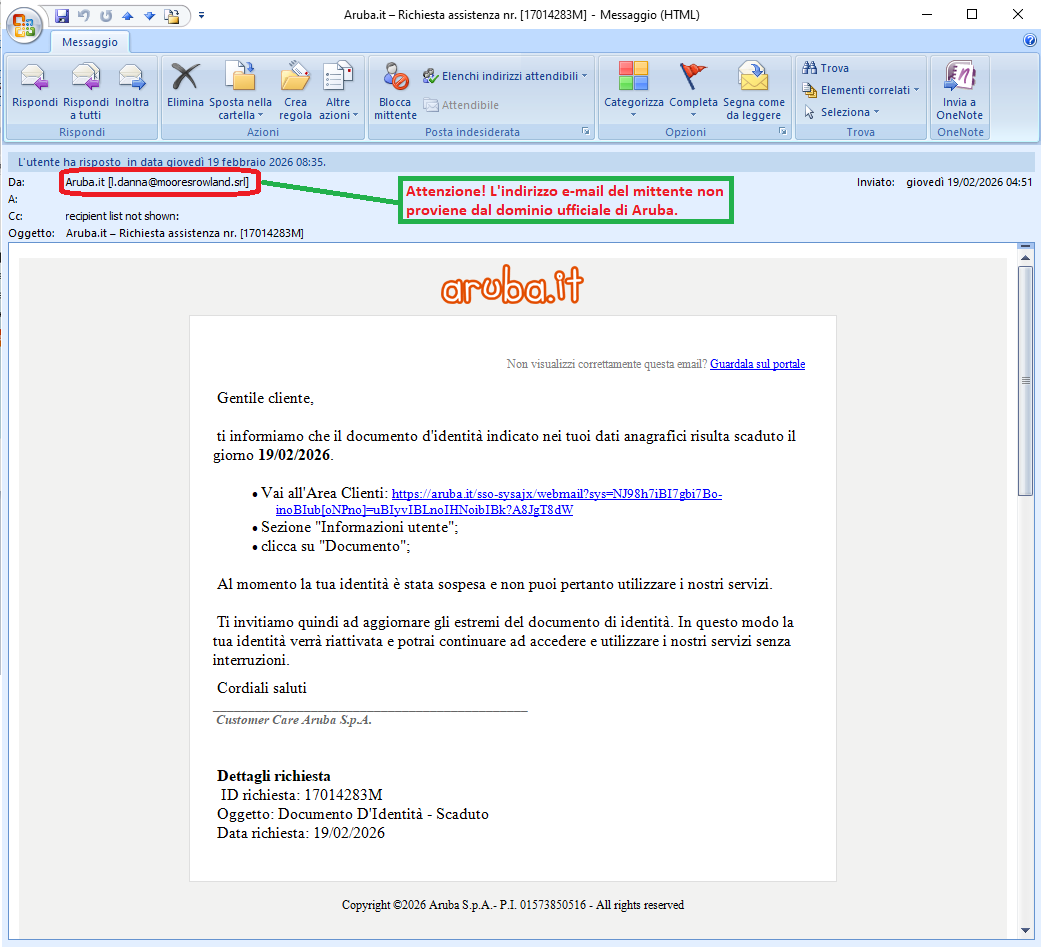 . This time, the message informs the recipient that the identity document indicated in his/her personal data expired on 19/02/2026.
. This time, the message informs the recipient that the identity document indicated in his/her personal data expired on 19/02/2026. If you are not yet using Vir.IT eXplorer PRO, it is advisable to install Vir.IT eXplorer Lite -FREE Edition- to supplement the antivirus in use to increase the security of your computers, PCs and SERVERS.
If you are not yet using Vir.IT eXplorer PRO, it is advisable to install Vir.IT eXplorer Lite -FREE Edition- to supplement the antivirus in use to increase the security of your computers, PCs and SERVERS. For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis
For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis