PHISHING INDEX
Below are the most common email phishing attempts detected by TG Soft's Anti-Malware Research Center in
March 2022:
29/03/2022 =>
Allianz Bank
21/03/2022 =>
Banca Carige
18/03/2022 =>
Aruba
18/03/2022 =>
Banco BPM
07/03/2022 =>
Smishing Intesa Sanpaolo
03/03/2022 =>
WhatsApp - Vincita iPhone (iPhone Winning)
These emails are intended to trick some unfortunate person into providing sensitive data - such as bank account information, credit card codes or personal login credentials - with all the possible easily imaginable consequences.
March 29, 2022 ==> Phishing Allianz
This new phishing attempt comes as a fake e-mail from
Allianz.
The message notifies the unsuspecting recipient that a message has been sent to him to confirm his phone number, so that he can continue using the online services
He must proceed to verify the number by 4/15/2022, otherwise his account will be blocked and he will have to contact one of Allianz Bank's branches. He can proceed by clicking on the following link:
Conferma il mio numero di telefono cliccando qui (Confirm my phone number by clicking here)
The alert message comes from an email address <lankshire(dot)farms(at)pei(dot)sympatico(dot)ca> unrelated to the Allianz domain, and contains thin, concise and extremely generic text, although, to make it more reliable, the Allianz logo was included.
Anyone who unluckily clicks on the link
Conferma il mio numero di telefono cliccando qui (Confirm my phone number by clicking here), will be redirected to an anomalous WEB page, which has already been reported as a DECEPTIVE PAGE/ WEBSITE. In fact it is run by cyber-criminals, whose goal is to get hold of your most valuable data, in order to use them for criminal purposes.
..
March 21, 2022 ==> Phishing Banca CARIGE
«SUBJECT: <
Conferma il numero di telefono!>
(Confirm the phone number!)
This new phishing attempt comes as a fake e-mail from
Banca CARIGE.
The message, seemingly from Banca CARIGE, invites the unsuspecting recipient to confirm his phone number, so that he can continue to use online services. The deadline is 03/30/2022, otherwise the account will be blocked and it will be necessary to go to the bank.
Verify your phone number by clicking on the link below:
Conferma il mio numero di telefono cliccando direttamente qui (Confirm my phone number by clicking directly here)
The alert message comes from an email address <cheryl(dot)young(at)bellaliant(dot)net> unrelated to the official domain of Banca CARIGE. There is also no account holder identification data as opposed to the official communications. On the other hand the logos of Banca CARIGE was introduced to make the message more reliable.
The purpose is to get the recipient to click on the link:
Conferma il mio numero di telefono cliccando direttamente qui (Confirm my phone number by clicking directly here)
which, we would like to point out, redirects to a page that has nothing to do with the Banca CARIGE website but which, as can be seen from the image below, is set up in a reasonably misleading way for an inexperienced user.
At a glance, the web page where we are redirected, seems trustworthy, mainly due to the graphic devices used, that can mislead the user. In fact, the site visually simulates quite well the
Banca CARIGE's portal.
We see, however, that the access page for Account management, is hosted on an address/domain that has nothing to do with
Banca CARIGE, as ew can seen from the image on the side (reported below):
https://agence[-]wordpress[-]boredaux[.]com/wp[-]includes/Requests/main/web
By entering login data into the
Banca CARIGE account to log into the bank account, the data will be sent to a remote server and used by cyber crooks with all the attached and related, easily imaginable, risks.
March 18, 2022 ==> Phishing Aruba "Problema di fatturazione" (Billing issue)
«SUBJECT: <
Aggiorna lo spazio di archiviazione dell'account >
(Update account storage space)
Here is another phishing attempt that comes as a fake communication from
Aruba.
The message informs the recipient that he has run out of message storage limits, and additional storage space is needed to save incoming messages to his
Aruba-hosted mailbox. The user is then asked to update the storage space to continue using his e-mail, via the proposed link:
ARCHIVIAZIONE (STORAGE )
Clearly, the well-known web hosting, e-mail and domain registration services company
Aruba, is unrelated to the mass sending of these e-mails, which are real scams whose goal remains, as always, to steal sensitive data of the unsuspecting recipient.
Examining the text of the message, we notice right away that the sender's e-mail address <
updates(at)esccoverage(dot)com> is anomalous and does not come from
Aruba's official domain.
We see, however, that the cyber-criminals, had the foresight to include the
Aruba logo to make the alert more reliable.
Anyone who unluckily clicks on the link
ARCHIVIAZIONE (STORAGE ), Will be redirected to a WEB page that has nothing to do with the mailbox server, but which has already been reported as a DECEPTIVE PAGE/ WEBSITE. In fact it is run by cyber-criminals, whose goal is to get hold of your most valuable data, in order to use them for illegal purposes.
March 18, 2022 ==> Phishing Banco BPM
«SUBJECT: <
Aggiornamento richiesto !>
(Update required !)
This new phishing attempt comes as a fake e-mail from
Banco BPM.
The message notifies the unsuspecting recipient that, in order to improve the security of their customers, they need to update their account details within 24 hours. You can proceed by clicking on the following link:
ACCEDI (LOGIN)
The alert message comes from an email address <inbox(at)kepplerseminare(dot)de> unrelated to the Banco BPM's domain contains extremely thin, concise and very generic text. However, to make it more reliable, identifying data of Banco BPM, such as the VAT number, were included. In addition, we can see that the message is set up in a graphically deceptive way for an inexperienced user.
Anyone who unluckily clicks on the link
ACCEDI (LOGIN), will be redirected to an anomalous WEB page, which has already been reported as a DECEPTIVE PAGE/ WEBSITE. In fact it is run by cyber-criminals, whose goal is to get hold of your most valuable data, in order to use them for illegal purposes.
March 07 ==> Smishing Intesa Sanpaolo
We examine below a new smishing attempt behind a fake text message from
Intesa Sanpaolo.
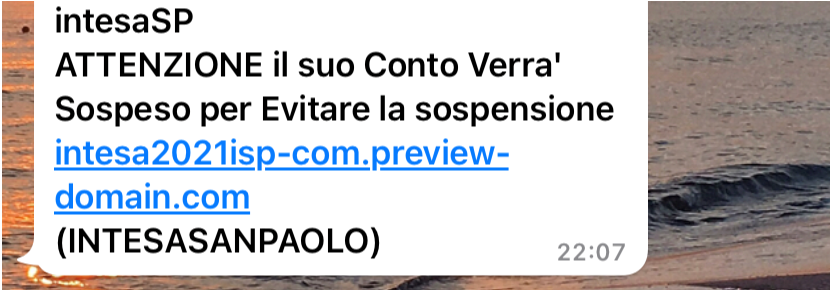
The message, which we quote on the side, alerts the unsuspecting recipient that his account will be suspended, without stating the reasons for the suspension. It therefore invites the user to check, by clicking on the proposed link, and to follow the procedure.
At first we notice that the alert, distinguished by its concise and essential layout, is generic; in fact, unlike in official communications of this type, no identifying reference (first and last name for example) of the
Intesa Sanpaolo account holder is mentioned.
The purpose clearly is to lead the user to click on the link:
https://intesa2021isp[-]com[.]preview[-]domain[.]com
As we can see from the image below, the web page to which the user is redirected by the link, simulates quite well the official
Intesa Sanpaolo's website and is set up in a reasonably deceptive way for an inexperienced user, both graphically and textually.
In order to reassure the user of the authenticity of the page, the cyber-criminals also had the foresight to include
Intesa Sanpaolo real references at the bottom of the site, including the VAT number.
Although the authentication FORM itself seems well done - requiring the entry of owner code, PIN, and phone number - we urge you to pay specific attention to the url address of the account management access page.
This is in fact hosted on an address/domain that has nothing to do with
Intesa Sanpaolo, and which we report below:
https://intesa2021isp[-]com[.]preview[-]domain[.]com
By entering your personal information on this FORM, to log into your
Intesa Sanpaolo checking account, this information will be sent to a remote server and used by cyber crooks with all the associated, easily imaginabl,e risks .
To conclude, we always urge you to be wary of any form that requires your confidential data, avoiding clicking on suspicious links. In fact these could lead to a counterfeit site, difficult to distinguish from the original one, where you shouldn't enter your sensitive data (ex: credit card data). You should always be sure of the website's origin before entering personal information, otherwise you deliver it to cyber crooks.
March 03, 2022 ==> Phishing WhatsApp Vincita IPhone 13 (IPhone 13 Winning)
SUBJECT: <
A new voicemail - Mar 2; 8 sec>
The following is a phishing attempt, hiding behind a fake e-mail from
WhatsApp.
This time the message, which we quote on the side, informs the victim that he has a new voice message to listen to, and that he can proceed through the proposed link:
autoplay
Examining the email we notice that the message, characterized by the concise and essential text layout, comes from an email address clearly not traceable to the
WhatsApp messaging App. <
darcellorigheschi(at)web01(dot)serv(dot)net(dot)mx>.
Anyone who unluckily clicks on the link
autoplay, will be redirected to a web page, which has nothing to do with WhatsApp's site, but seems more referable to Amazon's page. In fact its well-known logo is shown, and you are asked to participate in a short survey to win a fantastic iPhone 13 Pro...
"
Today, March 03, 2022, you have been chosen to participate in our survey. It will only take you a minute and you will receive a fantastic prize: Apple iPhone 13 Pro!"
|
The user, who is one of the 10 lucky winners drawn today, is asked below to participate in a short 4-question survey for a chance to win the new iPhone 13 Pro!
|
At the bottom are some comments from customers who appear to have already participated in the survey. The following questions are very general.
|
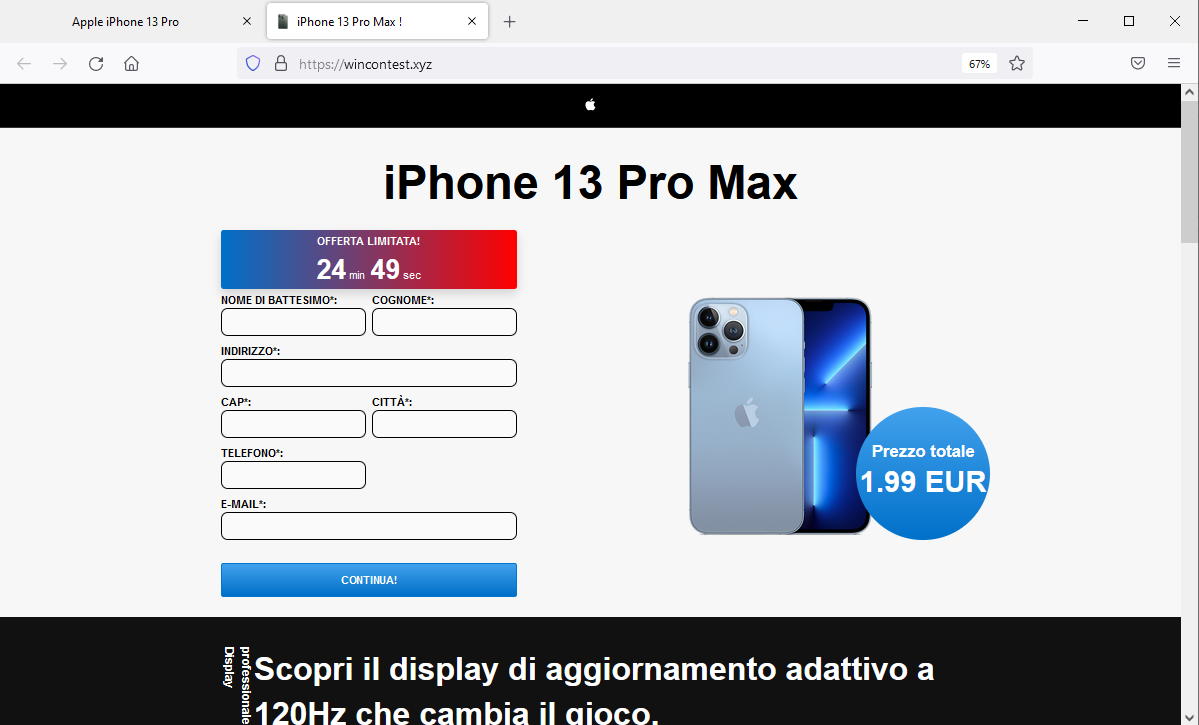
At the end of the questionnaire you will be sent back to another web page, where you are asked to choose a gift pack....After 2 attempts we finally manage to win our Apple iPhone 13 Pro!
|
The image at the bottom shows THE RULES to obtain the new smartphone, among which you are required to pay shipping costs between €1-5 to get an iPhone 13 Pro!
|
Surely, if so many users have been lucky, why not try your luck by filling out a simple survey!
The purpose is just to induce the user to enter his sensitive information, required for the iPhone 13 Pro shipping costs !
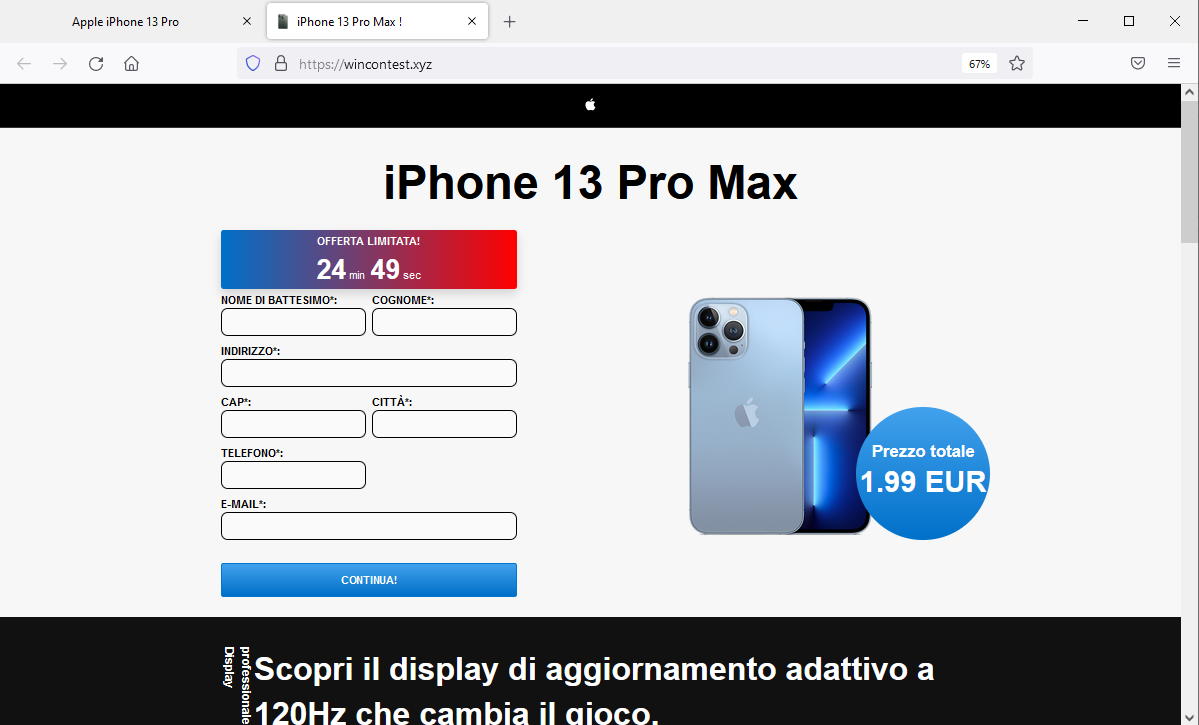
We notice from the side image, the url address of the web page hosting the sensitive data entry form:
https[:]//wincontest[.]xyz
In addition to be absolutely unrealted to
Amazon, it is completely unreliable.
To conclude, we always urge you to be wary of any email asking for confidential data, and avoid clicking on suspicious links which could lead to a counterfeit site, difficult to distinguish from the original, thus putting your most valuable data in the cyber crooks' hands for their use and profit.
A little bit of attention and glance, can save a lot of hassle and headaches..
We urge you NOT to be fooled by these types of e-mails, which, even though they use familiar and not particularly sophisticated approach techniques, if there is a resurgence, with reasonable likelihood more than a few unfortunates will be fooled.
We invite you to check the following information on Phishing techniques for more details:
03/02/2022 16:25:36 - Phishing: the most common credential theft attempts in February 2022...
04/01/2022 09:13:26 - Phishing: the most common credential theft attempts in January 2022....
03/12/2021 15:57:10 - Phishing: the most common credential theft attempts in December 2021..
04/11/2021 09:33:32 - Phishing: the most common credential theft attempts in November 2021.
07/10/2021 14:38:30 - Phishing: the most common credential theft attempts in October 2021.
10/09/2021 15:58:58 - Phishing: the most common credential theft attempts in September 2021..
05/08/2021 18:09:36 - Phishing: the most common credential theft attempts in August 2021..
01/07/2021 15:58:27 - Phishing: the most common credential theft attempts in July 2021 .....
07/06/2021 16:44:58 - Phishing: the most common credential theft attempts in June 2021..
12/05/2021 12:38:10 - Phishing: the most common credential theft attempts in May 2021..
06/04/2021 10:55:46 - Phishing: the most common credential theft attempts in April 2021.
04/03/2021 09:06:29 - Phishing: the most common credential theft attempts in March 2021
Try Vir.IT eXplorer Lite
 If you are not yet using Vir.IT eXplorer PRO, it is advisable to install Vir.IT eXplorer Lite -FREE Edition- to supplement the antivirus in use to increase the security of your computers, PCs and SERVERS.
If you are not yet using Vir.IT eXplorer PRO, it is advisable to install Vir.IT eXplorer Lite -FREE Edition- to supplement the antivirus in use to increase the security of your computers, PCs and SERVERS.
Vir.IT eXplorer Lite has the following special features:
- freely usable in both private and corporate environments with Engine+Signature updates without time limitation;
- interoperable with any other AntiVirus, AntiSpyware, AntiMalware or Internet Security already present on PCs and SERVERs. We recommend to use it as a supplement to the AntiVirus already in use as it does not conflict or slow down the system but allows to significantly increase security in terms of identification and remediation of infected files
- it identifies and, in many cases, even removes most of the viruses/malware actually circulating or, alternatively, allows them to be sent to the C.R.A.M. Anti-Malware Research Center for further analysis to update Vir.It eXplorer PRO;
- through the Intrusion Detection technology, also made available in the Lite version of Vir.IT eXplorer, the software is able to report any new-generation viruses/malware that have set in automatically and send the reported files to TG Soft's C.R.A.M
- proceed to download Vir.IT eXplorer Lite from the official distribution page of TG Soft's website.
VirIT Mobile Security AntiMalware ITALIAN for ALL AndroidTM Devices
VirIT Mobile Security, the Italian Anti-Malware software that protects Android™ smartphones and tablets, from Malware intrusions and other unwanted threats and empowers the user to safeguard their privacy with an advanced heuristic approach (Permission Analyzer)
 TG Soft makes VirIT Mobile Security available for free by accessing the Google Play Store market (https://play.google.com/store/apps/details?id=it.tgsoft.virit) from which you can pick up the Lite version, which can be freely used in both private and business settings.
TG Soft makes VirIT Mobile Security available for free by accessing the Google Play Store market (https://play.google.com/store/apps/details?id=it.tgsoft.virit) from which you can pick up the Lite version, which can be freely used in both private and business settings.
You can upgrade to the PRO version by purchasing it directly from our website: https://www.tgsoft.it/italy/ordine_step_1.asp
Acknowledgements
TG Soft's Anti-Malware Research Center would like to thank all users, customers, reseller technicians, and all people who have transmitted/reported material attributable to Phishing activities to our Research Center that allowed us to make this information as complete as possible...
Special thanks to Mr. Marco Mira for his active cooperation in sending us material for analysis.
How to send suspicious emails for analysis as possible phishing but also virus/malware or Crypto-Malware
You can submit materials to TG Soft's Anti-Malware Research Center safely and free of charge in two ways:
- Any suspect email can be sent directly by the recipient's e-mail, to the following mail lite@virit.com,choosing as sending mode "Forward as Attachment" and inserting in the subject section "Possible phishing page to verify" rather than "Possible Malware to verify"
- Save the e-mail to be sent to TG Soft's C.R.A.M. for analysis as an external file to the e-mail program used. The resulting file must be sent by uploading it from the page Send Suspicious Files (http://www.tgsoft.it/italy/file_sospetti.asp). Obviously if you want a feedback on the analysis of the data submitted, you have to indicate an e-mail address and a brief description of the reason for the submission (for example: possiible / probable phishing; possible / probable malware or other).
 For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis
For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis
We provide all this information to help you prevent credential theft, viruses/malware or, even worse, next-generation Ransomware / Crypto-Malware..
TG Soft's C.R.A.M. (Anti-Malware Research Center)


 We notice from the side image, the url address of the web page hosting the sensitive data entry form:
We notice from the side image, the url address of the web page hosting the sensitive data entry form: If you are not yet using Vir.IT eXplorer PRO, it is advisable to install Vir.IT eXplorer Lite -FREE Edition- to supplement the antivirus in use to increase the security of your computers, PCs and SERVERS.
If you are not yet using Vir.IT eXplorer PRO, it is advisable to install Vir.IT eXplorer Lite -FREE Edition- to supplement the antivirus in use to increase the security of your computers, PCs and SERVERS. TG Soft makes VirIT Mobile Security available for free by accessing the Google Play Store market (https://play.google.com/store/apps/details?id=it.tgsoft.virit) from which you can pick up the Lite version, which can be freely used in both private and business settings.
TG Soft makes VirIT Mobile Security available for free by accessing the Google Play Store market (https://play.google.com/store/apps/details?id=it.tgsoft.virit) from which you can pick up the Lite version, which can be freely used in both private and business settings. For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis
For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis