PHISHING INDEX
Below are the most common email phishing attempts detected by TG Soft's Anti-Malware Research Center in March 2024:
31/03/2024 =>
BRT
26/03/2024 =>
Meta
22/03/2024 =>
BRT
21/03/2024 =>
Aruba - Rinnova il dominio (Renew your domain)
13/03/2024 =>
Banco BPM
13/03/2024 =>
Istituto Bancario (Bank)
12/03/2024 =>
Mailbox Almost Full
11/03/2024 =>
Account di Posta (Email account)
06/03/2024 =>
Webmail
04/03/2024 =>
Aruba - Rinnova il dominio (Renew your domain)
01/03/2024 =>
LIDL
These emails are intended to trick some unfortunate person into providing sensitive data - such as bank account information, credit card codes or personal login credentials - with all the possible easily imaginable consequences.
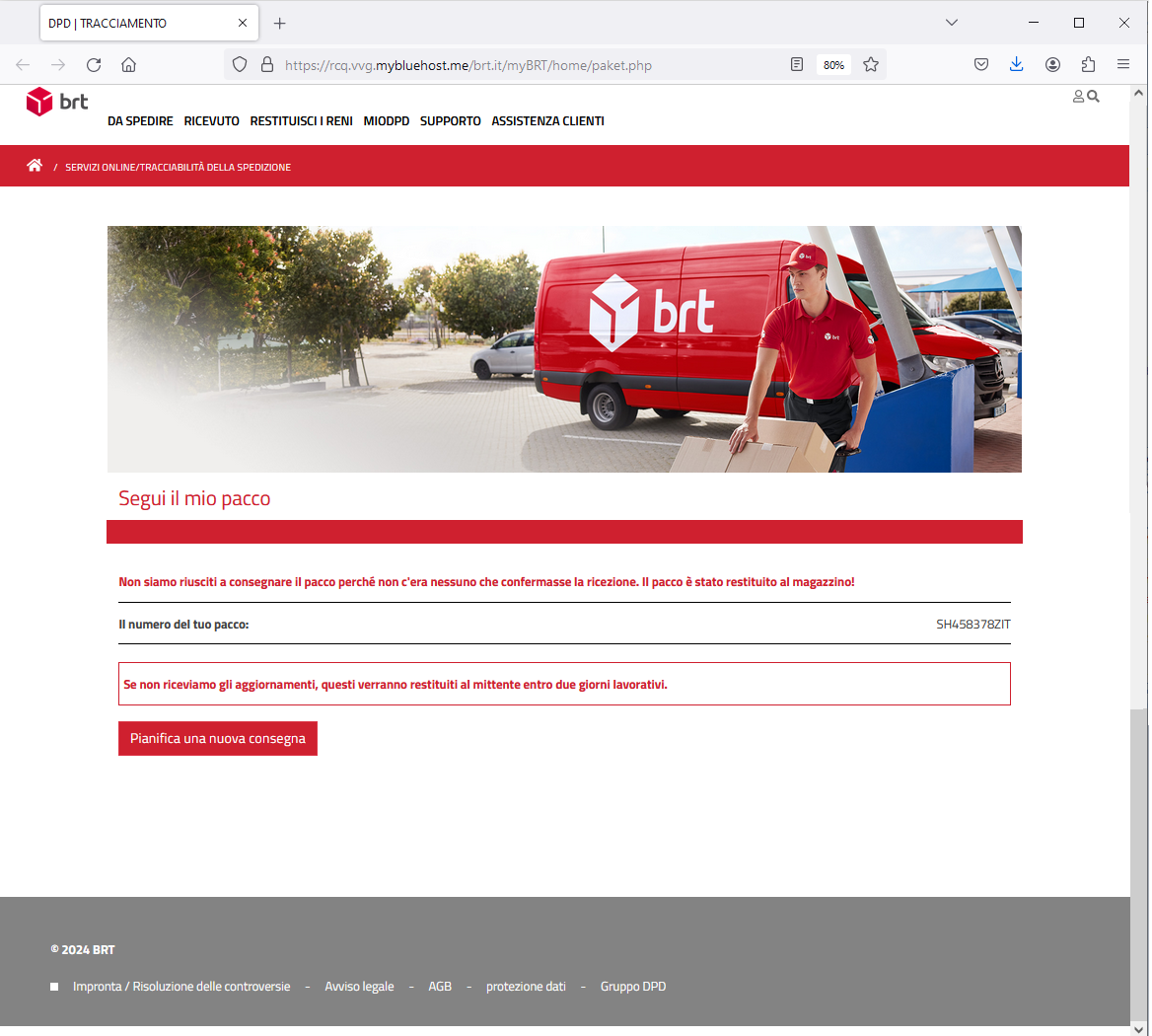
31 March 2024 ==> Phishing BRT
SUBJECT: <
Il tuo pacco non è stato consegnato.>
(Your package has not been delivered)
We analyze below another phishing attempt hidden behind a false communication from the
BRT courier company concerning the delivery of an alleged package.
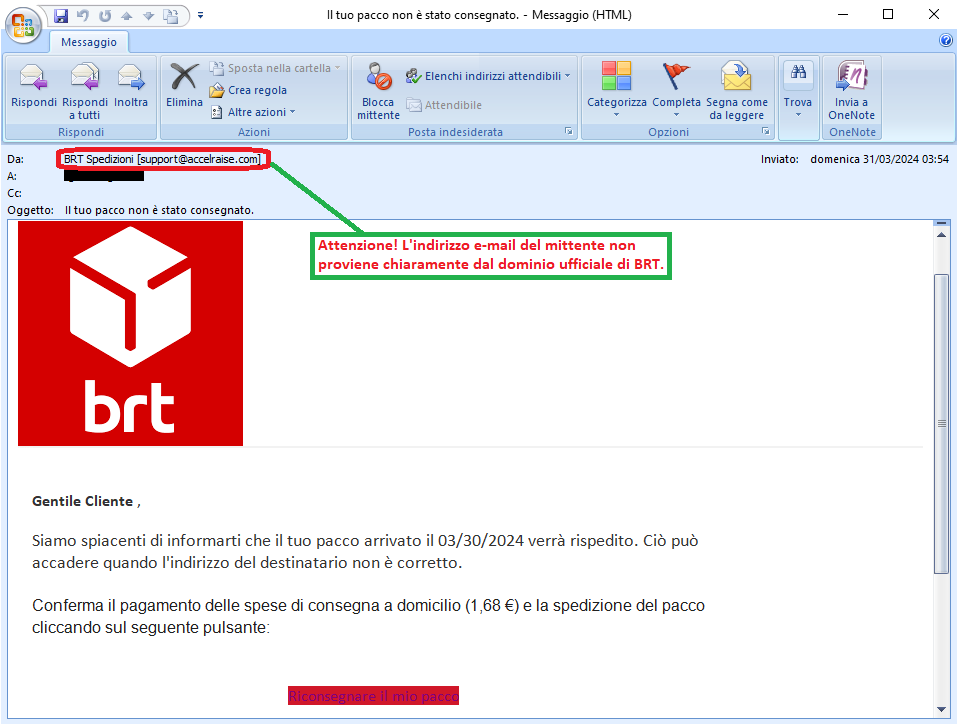
The message, which we reproduce on the side, refers specifically to a shipping being held in storage. In fact, it notifies the unsuspecting recipient that his package has not been delivered and that in order to receive it, the user has to reschedule the delivery and pay the shipping cost of 1.68 euros, using the following button:
Riconsegnare il mio pacco (Redeliver my package)
The message seems to come from the
BRT courier company and, to make it more reliable, the well-known logo has been included. We notice, however, that no identifying information about the shipment (such as the order number or tracking reference), is given.
The purpose is clearly to get the user to click on the provided link, which redirects to a web page designed, as always, to obtain the customer's sensitive data.
Let's analyze it in detail below.
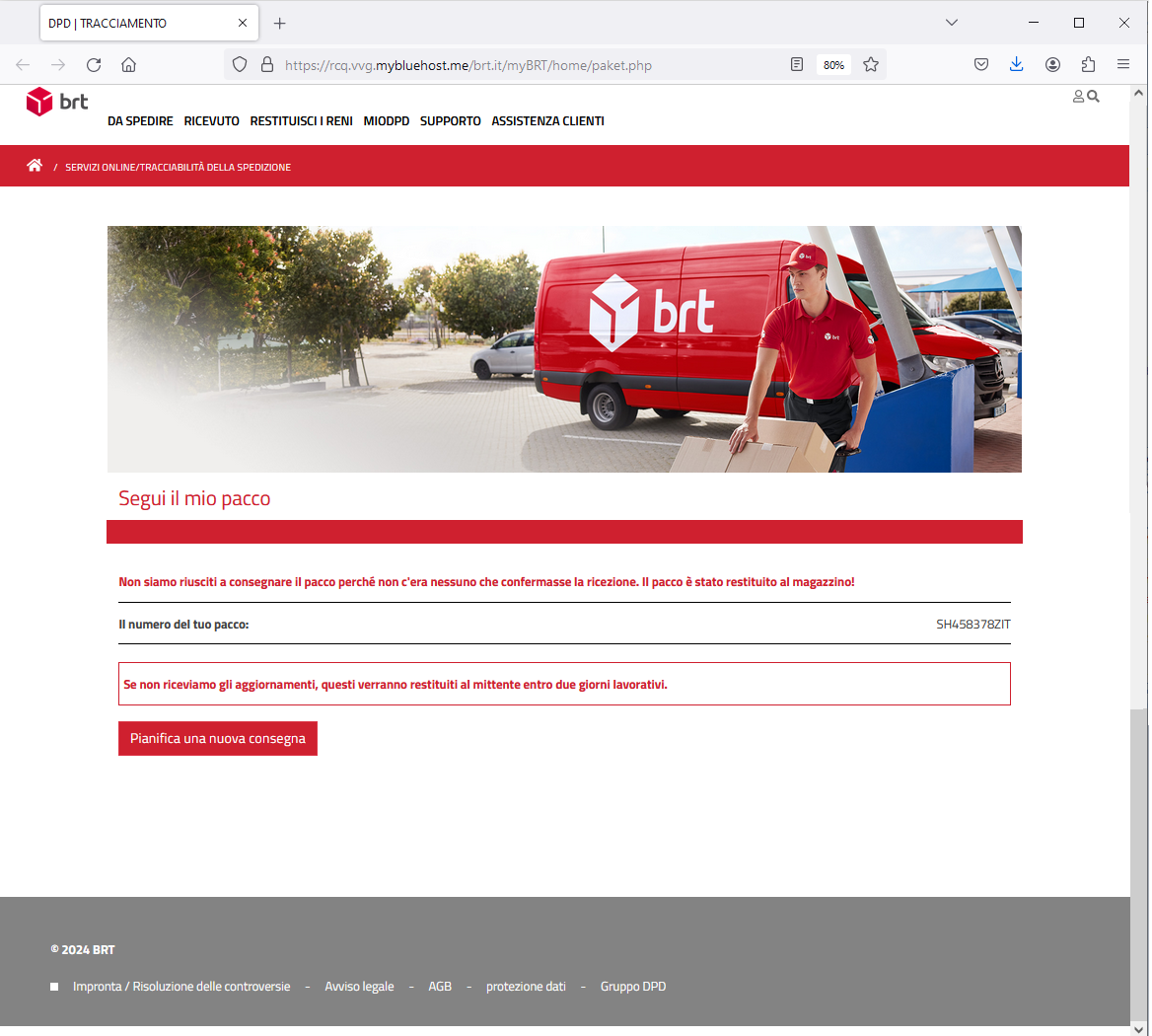
The link in the message directs us to a web page that simulates the official site of
BRT.
Although the site is graphically well done and includes the tracking number of the alleged parcel in storage <SH458378ZIT>, we observe that the url address present on the broswer bar <<https[:]//rcq[.]vvg[.]mybluehost[.]me/brt[.]it/myBRT/home/paket[.]php>> is anomalous and not traceable to BRT.
When we click on Pianifica una nuova consegna, (Schedule a new delivery), we are directed to a new screen where we are prompted to indicate our desired delivery.
Next, we select the date and click Continua (Continue). We are then presented with a new screen prompting us to update our parcel delivery information.
HERE IS THE SURPRISE! After clicking on
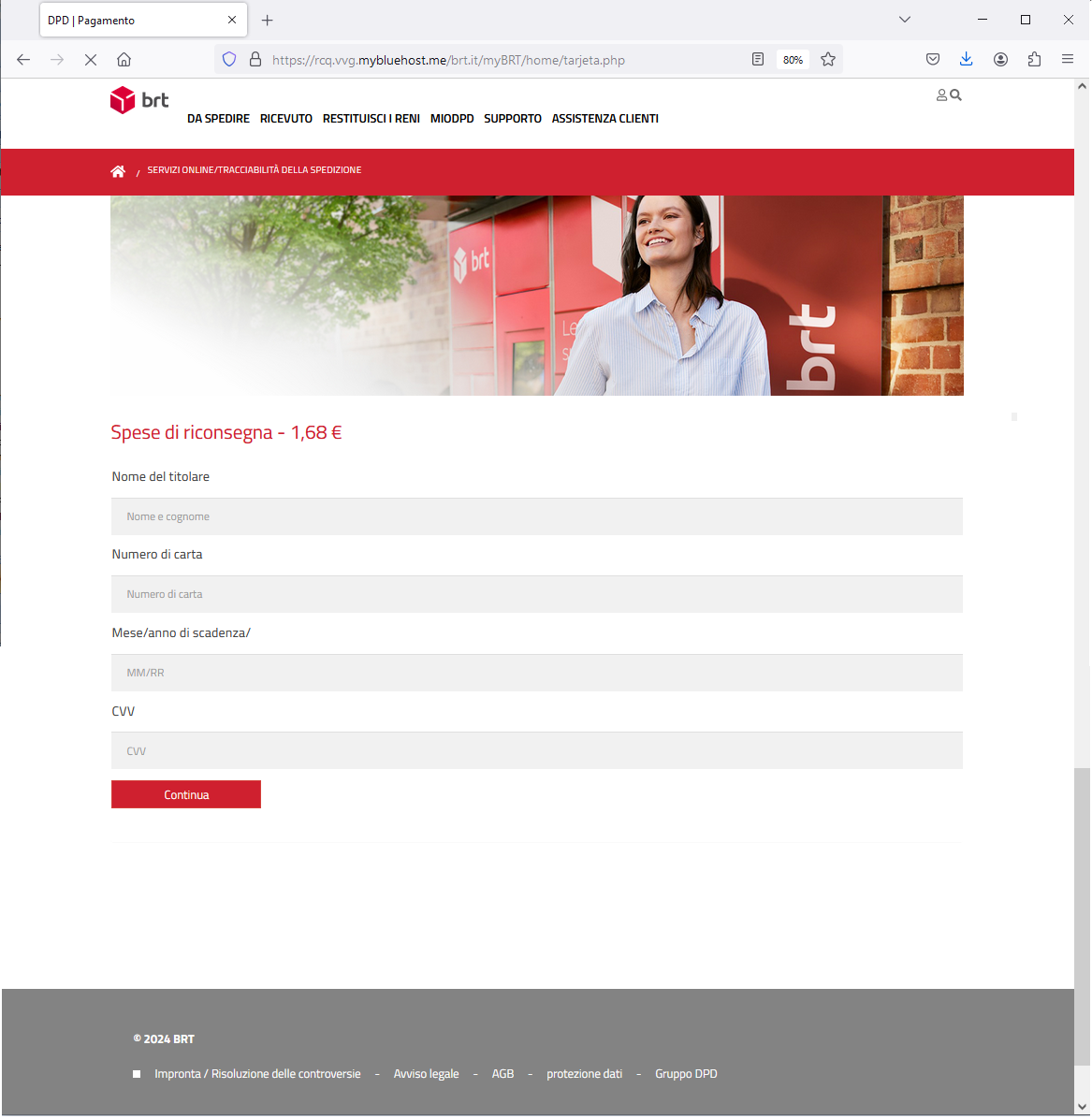
Continua (Continue), we are in fact redirected to a data-entry FORM that requires our credit card information to pay the shipping costs of the alerted package.
We observe that the page of the form is hosted on the following url address:
<<https[:]//rcq[.]vvg[.]mybluehost[.]me/brt[.]it/myBRT/home/tarjeta[.]php>>which is completely unreliable and not related to
BRT at all.
The purpose of the email is to induce the user to enter his personal data.
To conclude, we always urge you to be wary of any email that asks you to enter confidential data, and avoid clicking on suspicious links, which could lead to a counterfeit site difficult to distinguish from the original one. In fact in this way your most valuable data is put in the hands of cyber crooks and can be used for malicious purposes.
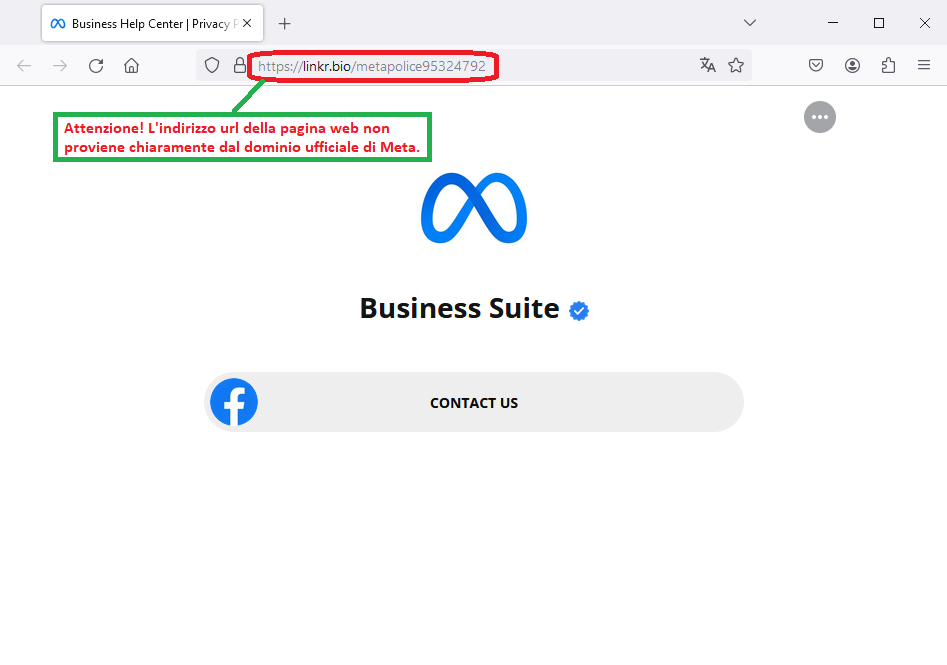
26 March 2024 ==> Phishing META for Business
SUBJECT: <Your IP issue detected in your advertising>
We analyze below a new phishing attempt concealed behind a false communication from
META, the company that manages the most popular social platforms.
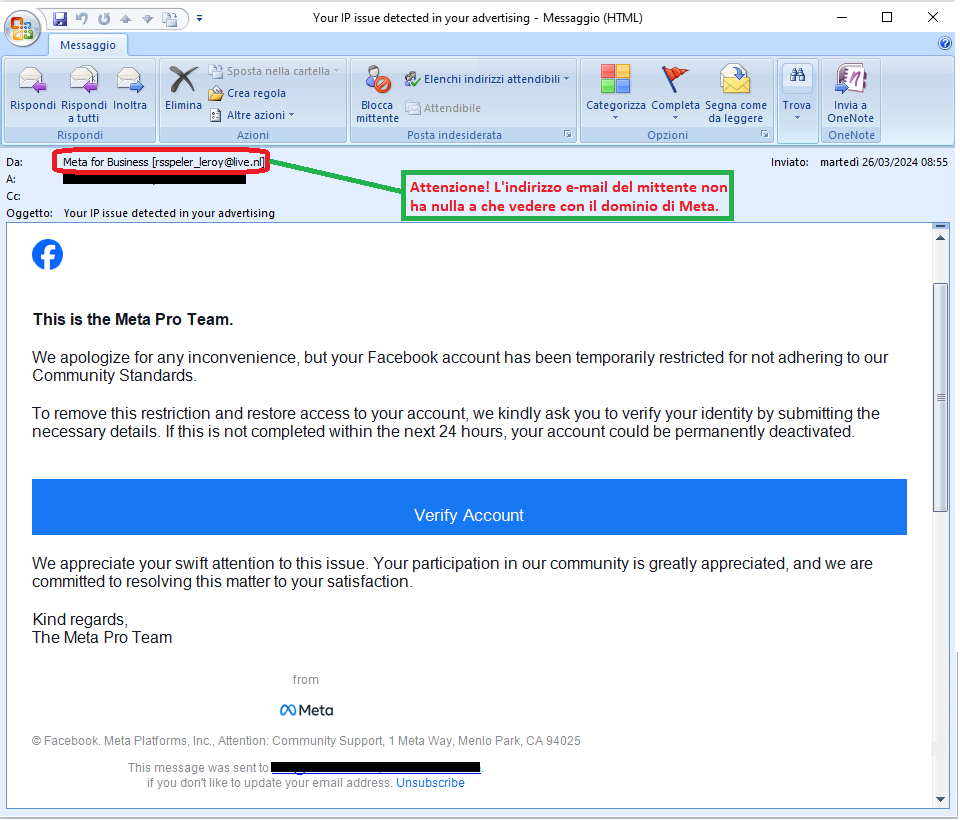
The message, which we quote on the side, alerts the recipient that his Facebook account has been temporarily restricted because the user has not adhered to community standards. It then invites the user to restore access and remove the restrictions by verifying his identity and agreeing to the community's terms. To update the data, the victim just needs to click on the following link:
Verify Account
The message seems to be from the
META platform; in fact, alleged identifying information is given, in addition to the well-known Facebook logo, to mislead the user. Analyzing the message, however, we notice that the sender's e-mail address <
rsspeler_leroy(at)live[.]nl> is not from the official domain of
META.
The purpose is clearly to lead the user to click on the proposed link, which redirects to a web page designed to steal the user's sensitive data.
Let us analyze it below in detail.
From the link in the message we are redirected to a web page simulating the official site of
META. Although the site is graphically deceptive, we see that the url address on the broswer bar <<https[:]//linkr[.]bio/metapolice95324792>> is anomalous and not traceable to
META.
If we click on .Contact us we are redirected to a new graphically well-done screen that seems to be traceable to the Facebook Business Help Center, but which, again, is hosted on an anomalous url address: <<https[:]/business-help-term-9741239845[.]surge[.]sh/help/contact/605580619591675>>.
After selecting one of the suggested items, we are presented with a new screen, prompting us to enter our personal information (Phone, E-mail and date of birth) for assistance.
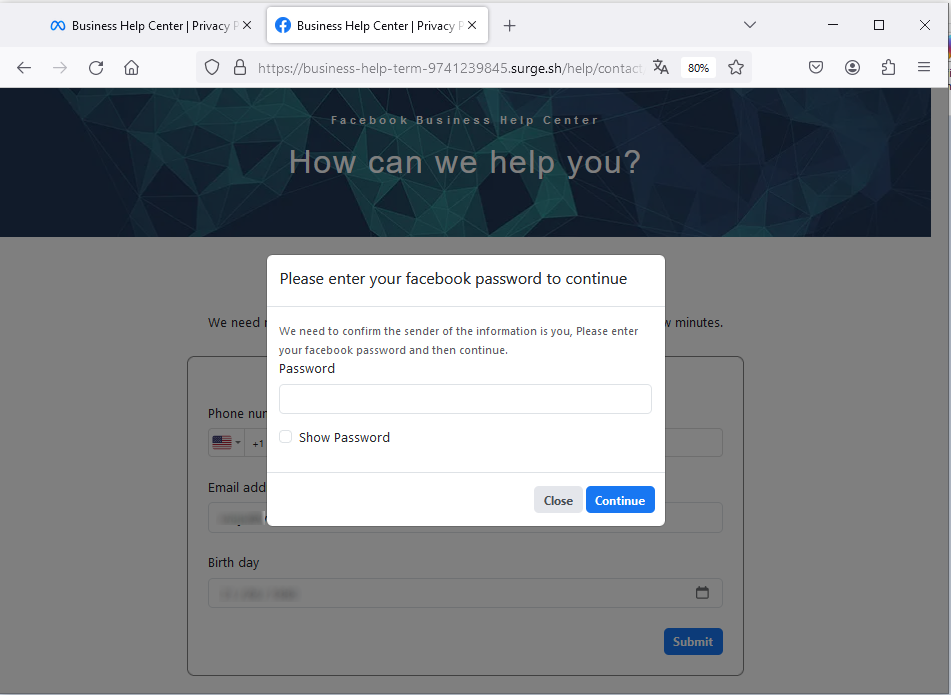
When we enter our data and click
Submit, we are prompted to enter our Facebook account password to confirm our identity.
Clearly, the well-known
META company is unrelated to the mass sending of these emails, which are real scams whose goal remains, as always, to steal sensitive data of the unsuspecting recipient.
The purpose is to induce the user to enter the login password for his/her account, which will be stolen and used by cyber criminals.
22 March 2024 ==> Phishing BRT
SUBJECT: <
BRT - Giarcenza 580301>
We analyze below a new phishing attempt concealed behind a false communication from
BRT, concerning the delivery of an alleged package.
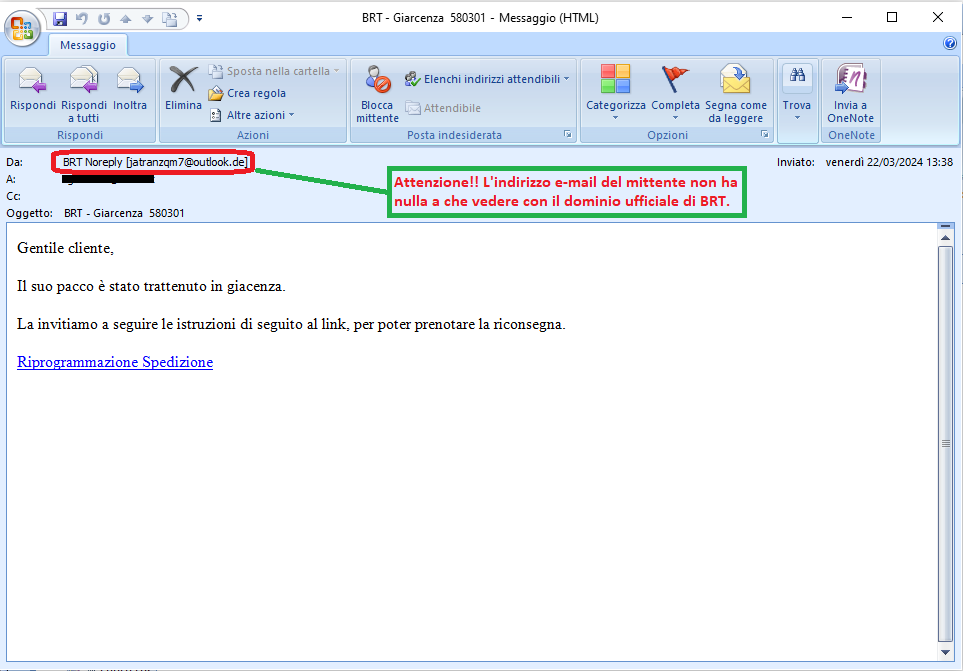
The message, which we quote on the side, refers to a package in storage. In fact, it notifies the unsuspecting recipient the instructions to reschedule the delivery of his package, via the link below:
Riprogrammazione Spedizione (Rescheduling Shipping)
The message, based on the subject line of the e-mail, seems to be from the
BRT courier company. We notice, however, that no identifying information is given either about the shipment - such as the order number or tracking reference - or even about
BRT.
The purpose is clearly to lead the user to click on the proposed link, which redirects to a web page that, as always, requires the entry of the user's sensitive data in order to steal them.
Let us analyze it below in detail.
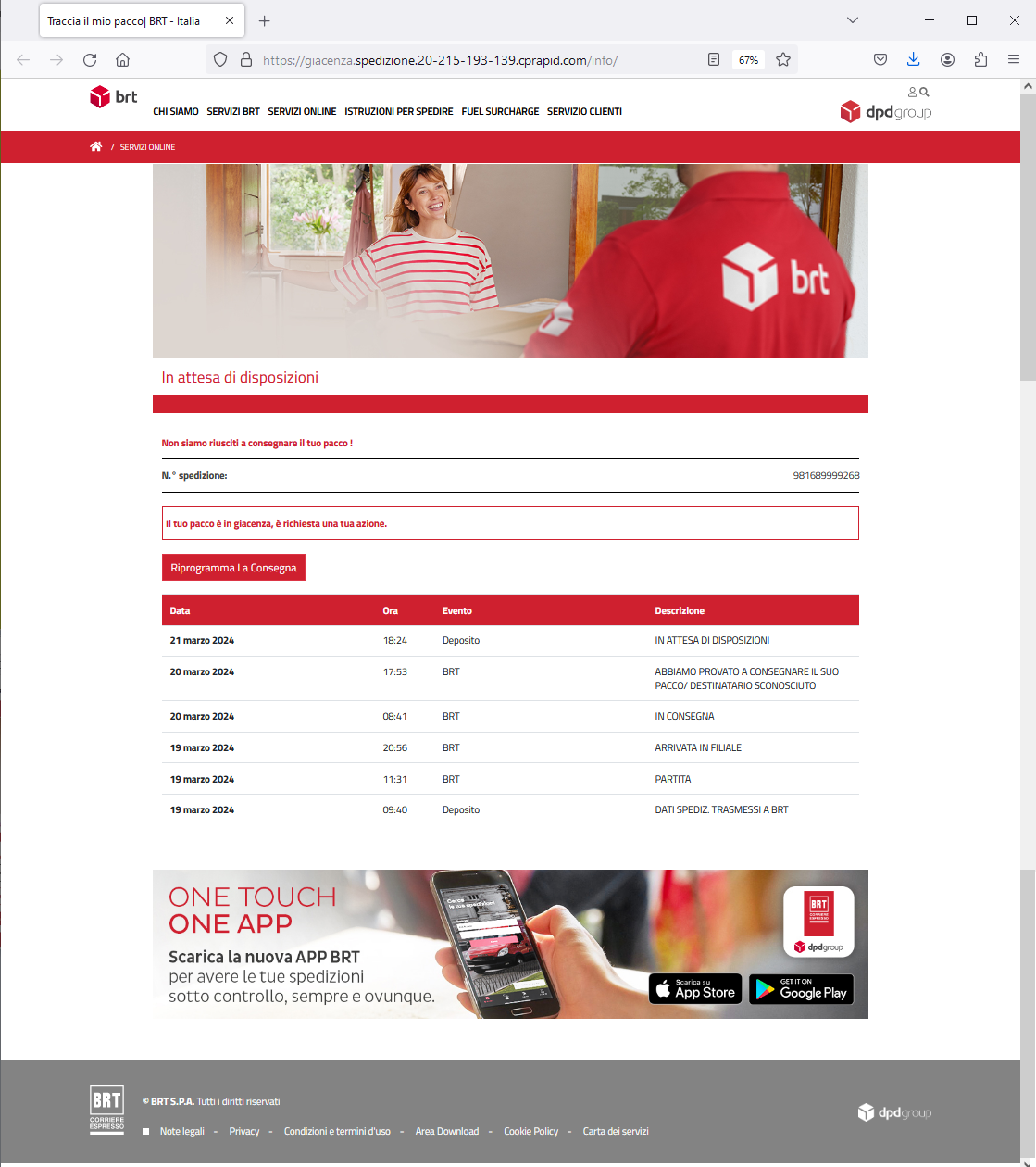
From the link in the message we are redirected to a web page that simulates the official website of
BRT. Although the site is graphically well done and includes the shipping number of the alleged package in storage <981689999268> along with shipping details with dates and time stamped, we notice that the url address <<
https[:]//storage[.]shipping[.]20-215-193-139[.]cprapid[.]com/info/>> is anomalous and not traceable to
BRT.
If we click on Riprogramma La Consegna (Reschedule Delivery), we are redirected to a new screen asking to specify two delivery dates for the package, with the associated shipping costs..
When we select the date and click Continua (Continue), we are presented with a new screen that prompts us to update our parcel delivery information.
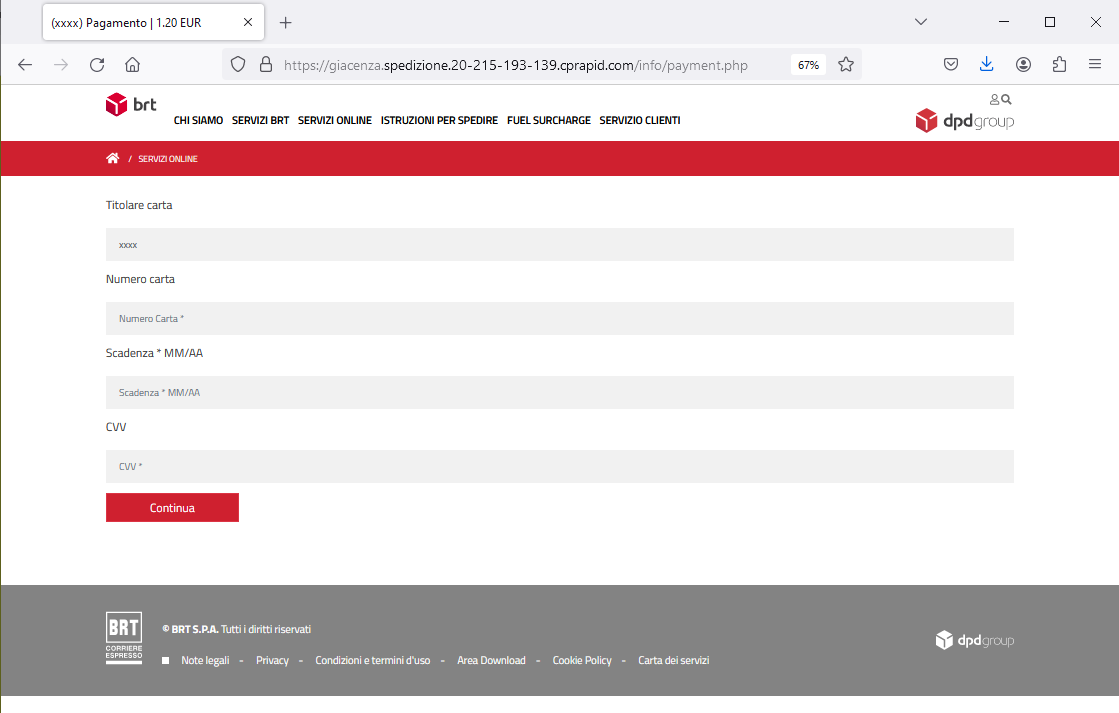
HERE IS THE SURPRISE! After clicking
Continua (Continue), we are in fact redirected to a data-entry FORM, that requires credit card information to pay the shipping costs of the package subject of the alert..
We see that the form page is hosted on the following url address:
<<https[:]//warehousing[.]shipping[.]20-215-193-139[.]cprapid[.]com/info/payment[.]php>> which is completely untrustworthy and is not related to
BRT at all.
The purpose of the email is to induce the user to enter his personal data.
To conclude, we always urge you to be wary of any email that asks you to enter confidential data, and avoid clicking on suspicious links, which could lead to a counterfeit site difficult to distinguish from the original one. In fact in this way your most valuable data is put in the hands of cyber crooks and can be used for malicious purposes.
21 March 2024 ==> Phishing Aruba - Rinnova il dominio (Renew your domain)
SUBJECT: <
Rinnova il tuo dominio ****** in scadenza>
(Renew your expiring ****** domain)
Phishing attempts, pretending to be communications from the
Aruba brand, continue this month.
The message warns the recipient that his domain hosted on Aruba, linked to his e-mail account, will expire on 22/03/2024. It then asks him to manually renew it to avoid the deletion of the account and thus the deactivation of all services associated with it, including mailboxes, and the chance to receive and send messages.
It then invites the user to complete the renewal order by choosing the most convenient payment method, through the following link:
RINNOVA CON UN CLIC (RENEW WITH A CLICK)
Clearly, the well-known web hosting, e-mail and domain registration services company Aruba, is unrelated to the mass sending of these e-mails, which are real scams whose goal remains, as always, to steal sensitive data of the unsuspecting recipient.
Analyzing the text of the message, we notice right away that the sender's e-mail address <
communications-aruba(at)spiss[.]it> is not from
Aruba's official domain.
In order to induce the victim to proceed with the renewal of his mailbox in a timely manner, the expiration date of 22/03/2024 is indicated. Since the mail was delivered on 21/03/2024, there is not much time to carry out the renewal and prevent the deactivation of services.
The user is then offered to activate auto-renewal to get rid of deadlines and avoid thinking about service renewals. The procedure is simple and can be activated from the following link:
ATTIVA RINNOVO AUTOMATICO (ACTIVATE AUTOMATIC RENEWAL)
Anyone who unluckily clicks on the link
RINNOVA CON UN CLIC (RENEW WITH A CLICK), will be redirected to an anomalous WEB page, which has already been reported as a DECEPTIVE WEBSITE/PAGE. In fact it is run by cyber-criminals who want to get hold of your most valuable data, in order to use it for illegal purposes.
13 March 2024 ==> Phishing Banco BPM
«
SUBJECT: <
seguire le istruzioni per evitare la sospensione dei suoi servizi online>
(Follow the instructions to avoid suspension of your online services)
The following is another phishing campaign spreading through an e-mail exploiting stolen graphics or similar to the graphics of a well-known national banking institution (in this case Banco BPM). Hence it tries to pass itself off as an official communication, in order to induce the unsuspecting recipient to enter his data, and fall into a social engineering trap.
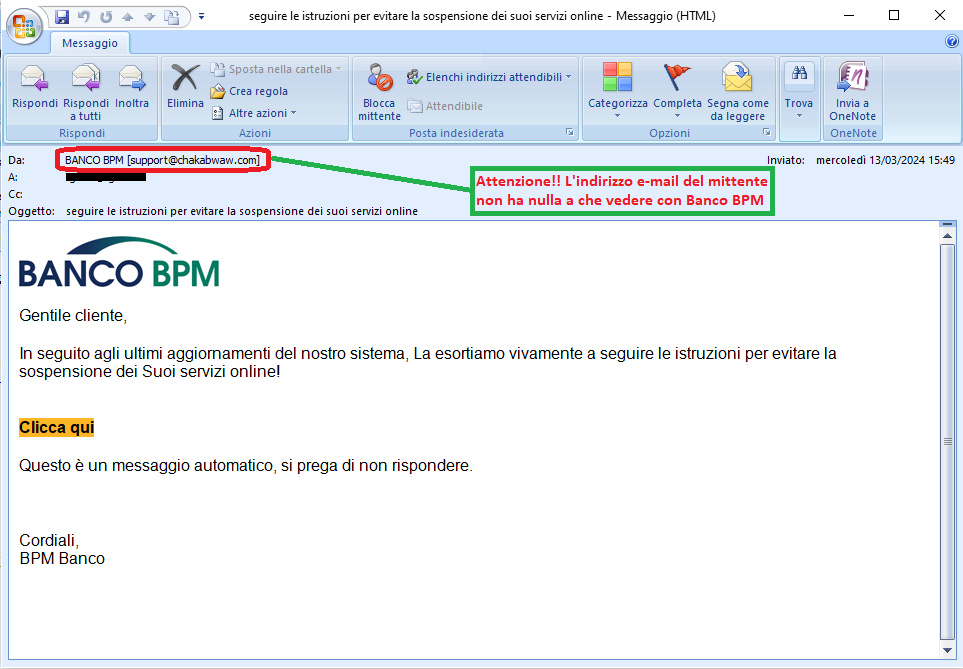
The message notifies the victim that, due to the latest updates to their systems, in order to continue using their services and avoid suspension, he must follow the instructions given. It then invites the user to activate the new security system, through the following link:
Clicca qui (Click here)
We can see right away that the alert message comes from an e-mail address <support(at)chakabwaw(dot)com> very suspicious and contains a very generic text, although the cybercriminal had the graphic foresight to include the well-known Banco BPM logo that could mislead the user.
The purpose is to lead the recipient to click on the
Clicca qui (Click Here) link that redirects to a page unrelated to the official site but which has already been reported as a deceptive page/SITE. In fact it is run by cyber-criminals who want to get hold of your most valuable data, in order to use it for illegal purposes.
13 March 2024 ==> Phishing Istituto Bancario (BANK)
SUBJECT: <
Avviso! >
(Warning!)
We find again this month the phishing campaign that spreads through an e-mail exploiting stolen graphics or similar to the graphics of a well-known national banking institution. Hence it tries to pass itself off as an official communication, in order to induce the unsuspecting recipient to enter his data, and fall into a social engineering trap.
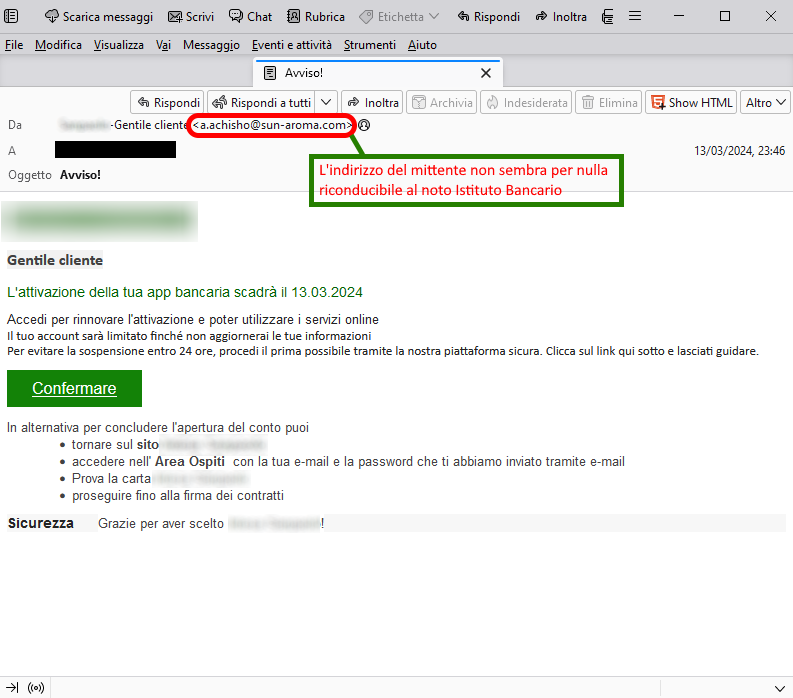
The message notifies the unsuspecting recipient that the banking app activation is expiring on 13/03/2024 and that to renew it he has to log in by clicking on the
Confermare (Confirm) link.
We can see right away that the alert message comes from an e-mail address <
a(dot)achisho(at)sun-aroma(dot)com> that is highly suspicious and contains a very generic text, although the cybercriminal had the graphic foresight to include the well-known logo of the banking institution, that could mislead the user.
The purpose is to get the victim to log in and renew the activation of his or her banking app.
To renew, he needs to click on the following link
Confermare (Confirm).
Anyone who unluckily clicks on the
Confermare (Confirm) link, will be redirected to an anomalous WEB page, which is unrelated to the official website of the well-known Banking Institution.
From the image on the side we can see that the web page is graphically well done, and pretty well simulates the official website of the banking portal.
We also observe other sub-menus such as Persone (People) and Famiglie (Families), Giovani (Youth), Business, which identify the type of user... all of this with the aim of further reassuring the user about the reliability of the portal, although many links on the page do not lead to the expected pages.
Given these considerations, we urge you to pay close attention to any misleading details, and keep in mind that before proceeding to enter sensitive data - in this case, home banking credentials i.e., Holder Code and PIN - it is crucial to analyze the url address of the authentication form.
The landing page in this case is hosted on the url address:
srv209846[.]hoster[-]test[.]ru/it/conto/
which is unrelated to the official website of the well-known banking institution.
This deceptive PAGE/ WEBSITE is run by cyber-criminals whose goal is to get hold of your most valuable data in order to use it for malicious purposes.
12 March 2024 ==> Phishing Mailbox Almost Full
SUBJECT: <
RE: MAIL ALMOST FULL>
We analyze below another phishing attempt that aims to steal email account login credentials.
The message, in English, informs the recipient that the space on his/her e-mail account is almost full and therefore invites him to free up space by deleting e-mails in order to receive new messages, via the link below:
CLEAR STORAGE
Analyzing the email, we notice that the message comes from an email address <
account(dot)service(at)mailbox(dot)com> that could mislead the victim, as it is similar to
Mailbox's domain, but it does not actually come from the official domain.
Anyone who unluckily clicks on the link
CLEAR STORAGE will be redirected to an anomalous WEB page, which has already been reported as a DECEPTIVE WEBSITE/PAGE. In fact it is run by cyber-criminals who want to get hold of your most valuable data, in order to use it for illegal purposes.
11 March 2024 ==> Phishing Account Posta Elettronica ((Phishing Email Account))
SUBJECT: <
Verifica password>
(Password verification)
We analyze below a new phishing attempt that aims to steal email account login credentials
The message, in English, informs the recipient that his/her e-mail account password will expire in 24 hours. It then invites him to confirm his password to continue using it, through the following link:
Conferma password (Confirm Password)
Analyzing the e-mail we see that it seems to come from the recipient's address. This could mean that the mail account was actually compromised or that a label was used to simulate the victim's address.
Anyone who unluckily clicks on the
Conferma password (Confirm Password), link will be presented with the screen shown in the side image.
As we can see we are redirected to a site that is unrelated to the provider of the mail account. This is an anomalous address/domain, which we report below:
https[:]//www[.]24people[.]nl....
Given these considerations, we point out that you should NEVER enter your credentials on sites whose origin you do not know, as they will be sent to a remote server and used by cyber crooks with all the associated easily imaginable risks
06 March 2024 ==> Phishing Webmail
SUBJECT: <
Routine Mail Server Upgrade>
We analyze below the phishing attempt that aims to steal the victim's e-mail account credentials
The message, in English, informs the recipient that his email account is out of date and he can't send or receive messages. It then invites him to reconfirm the account to avoid delayed incoming messages, via the following link:
Confirm your Email
Analyzing the email, we notice that the message comes from an email address that could mislead the victim, as it appears to come from the recipient's domain <noreply(at)*****(dot)it>, but in fact the real sender has been disguised.
This is definitely anomalous and should, at the very least, make us suspicious
Anyone who unluckily clicks on the link
Confirm your Email, will be redirected to an anomalous WEB page, which as you can see from the side image,is unrelated to the e-mail account manager.
The page where you are redirected, to enter your mail account credentials, is hosted on an anomalous address/domain, which we report below:
https[:]//cloudflare-ipfs[.]com/ipfs/bafybeieoxvl6l3tnajmoaofistnpm46pivaes....
We always urge you to be careful and not to enter your personal data and/or passwords on forms hosted on counterfeit web pages, as they will be sent to a remote server and used by cyber crooks with all the associated easily imaginable risks.
04 March 2024 ==> Phishing Aruba - Rinnova il dominio (Renew your domain)
SUBJECT: <
Rinnovo automatio del dominio xxxxx.it non riuscito> (
Automatic renewal of domain xxxxx.it failed)
Phishing attempts, pretending to be communications from
Aruba, continue this month.
The message informs the recipient that his domain hosted on
Aruba linked to his e-mail account will expire on 05/03/2024. It then warns him that if the domain is not renewed, it will be deactivated along with all the services associated with it, including email accounts. He will therefore no longer be able to receive and send messages.
It then invites the user to log in to renew services, via the following link::
RINNOVA IL DOMINIO (RENEW THE DOMAIN)
Clearly, the well-known web hosting, e-mail and domain registration services company
Aruba, is unrelated to the mass sending of these e-mails, which are real scams whose goal remains, as always, to steal sensitive data of the unsuspecting recipient.
Analyzing the message, we notice right away that the sender's e-mail address<
noreply(at)server110325[.]netart[.]com> is not from
Aruba's official domain.
In order to induce the victim to promptly proceed with the renewal of his mailbox, an expiration date of 05/03/2024 is indicated. Since the mail was delivered on 04/03/2024, there is not much time available to carry out the renewal and prevent the deactivation of services. The technique of stating a deadline to conclude the procedure is intended to scare the user with the threat of deactivation of the mailbox, in order to push the him/her to act immediately and without much thought.
Anyone who unluckily clicks on the link
RINNOVA IL DOMINIO (RENEW THE DOMAIN) will be redirected to the displayed page.
As we can see, first of all, the landing page, unlike what we expect, does not redirect to the access form to login to
Aruba's RESERVED AREA but hosts an online payment form that seems to rely on the
BancaSella circuit. Here you are directly prompted to enter your credit card information to complete the payment of the modest sum of Euro 5.99......
Although the user may be pushed to quickly complete the transaction by haste and the fear of email box suspension, if we just look at the url address shown on the broswer bar, we can realize that the payment form does not reside on the official domain of
Aruba or even
BancaSella:
https[:]//arubahost[.]assistenzastaff[.]net/0121/9.....
We therefore urge you not to rush and pay attention to every detail, even trivial ones.
By proceeding to enter the requested data, in this case your credit card details specifically, it will be delivered to the cyber criminals masterminding the scam who will use it for criminal purposes.
01 March 2024==> Phishing LIDL
SUBJECT: <
Festeggiamo l'anniversario di Lidl con un Samsung Galaxy S24 in omaggio >
(Let's celebrate Lidl's anniversary with free Samsung Galaxy S24)
Below we analyze the scam attempt that hides behind a false communication from
LIDL, the well-known supermarket.
This is a promotional message that seems to propose an unmissable opportunity. The lucky user was selected, on the anniversary of the supermarket chain, to participate in a survey and win a prize: a Samsung Galaxy S24...or at least that's what it seems.
Certainly for many inexperienced users this phishing is a real decoy.
Clearly,
LIDL is unrelated to the mass mailing of these malicious campaigns, which are real scams whose goal remains, as always, to steal sensitive data of the unsuspecting recipient.
To avoid misunderstanding we underline that this is in fact a phishing attempt aimed at stealing your personal data.
So keep your eyes open ... all it takes to avoid unpleasant incidents is a little attention and a quick glance.
When we analyze the email, we notice that the message comes from an email address <abdelfattah[dot]ammari[at]ump[dot]ac[dot]ma> not traceable to LIDL . This is definitely anomalous and should, at the very least, make us suspicious. However, if we go ahead and click on the link provided, here is what happens:
we are redirected to a landing page that, although graphically well done (with misleading images and the authentic
LIDL logo ) does not seem trustworthy at all.
In fact, the survey to obtain the prize, is hosted on an anomalous address/domain.
Here is the web page:
"https[:]//xforegone[.]lat/855c92.....''
which has no connection with
LIDL.
Cyber criminals masterminding the scam, try to induce the user to quickly finish the survey by making him believe that only few people can win and the gifts are about to run out. There is also a countdown timer at the bottom of the screen, which however, if stopped - as we simulated - will start over immediately. This is a rather strange thing.
Moreover, many comments from customers who supposedly participated in the survey, have been reported to give more credibility to the message. They are all reassuring testimonials/feedback about the actual delivery of the winnings that confirm the trustworthiness of the message, and some of them even include photos of the received prize.
Surely if so many users were lucky why not try our luck by filling out a simple survey?!
Clicking on
INIZIA IL SONDAGGIO (START THE SURVEY), you are redirected to the next screens, where you are asked to answer 8 questions.
Here is specifically question 1/8. These are very general questions focused on the degree of satisfaction with the services offered by
LIDL, and on the daily habits of consumers. Here, too, there is a countdown to prompt the user to quickly finish the process for the award.
At the end of the survey we can finally claim our prize: a Samsung Galaxy S24 that would be worth 1182.58 Euros but costs us 0.We only have to pay shipping costs, which are supposed to be small.
But let's hurry. There seem to be only 3 left in stock...
''Congratulazioni! Abbiamo riservato (1) Samsung Galaxy S24 esclusivamente per te.''
(Congratulations!!! We have reserved (1) Samsung Galaxy S24 exclusively for you.')
Here we go: in fact, all you need to do is to enter your shipping address and pay the shipping cost, and in 5-7 business days the prize will be delivered....
Then you are redirected to a further page, to enter your shipping address and to pay the shipping charges, as shown in the image below.
The page hosting the data entry form looks graphically well done and misleading. A detailed description of the award is provided, complete with technical specifications. Too bad that in order to complete it all, it is necessary to pay the shipping costs, which, although modest, arguably involve entering credit card information in order to complete the purchase.
The page where we are redirected, to enter our personal data, is hosted on a new anomalous address/domain, which we report below:
https[:]//collectedall[.]com/c/h7qCb.....
To conclude, we always urge you to be wary of advertisements/promotional messages that boast of "giving away" valuables, and to avoid clicking on suspicious links, which could lead to a counterfeit site that steals your most sensitive data.
A little bit of attention and glance, can save a lot of hassles and headaches..
We urge you NOT to be fooled by these types of e-mails, which, even though they use familiar and not particularly sophisticated approach techniques, if there is a resurgence, with reasonable likelihood more than a few unfortunates will be fooled.
We invite you to check the following information on phishing techniques for more details:
06/02/2024 08:55 - Phishing: the most common credential and/or data theft attempts in February 2024...
02/01/2024 16:04 - Phishing: the most common credential and/or data theft attempts in January 2024...
11/12/2023 09:39 - Phishing: the most common credential and/or data theft attempts in December 2023...
03/11/2023 08:58 - Phishing: the most common credential and/or data theft attempts in November 2023...
03/10/2023 16:35 - Phishing: the most common credential and/or data theft attempts in October 2023...
05/09/2023 10:35 - Phishing: the most common credential and/or data theft attempts in September 2023...
01/08/2023 17:33 - Phishing: the most common credential and/or data theft attempts in August 2023...
03/07/2023 10:23 - Phishing: the most common credential and/or data theft attempts in July 2023...
07/06/2023 15:57 - Phishing: the most common credential and/or data theft attempts in June 2023...
03/05/2023 17:59 - Phishing: the most common credential and/or data theft attempts in May 2023...
05/04/2023 17:34 - Phishing: the most common credential and/or data theft attempts in April 2023...
03/03/2023 16:54 - Phishing: the most common credential and/or data theft attempts in March 2023..
Try Vir.IT eXplorer Lite

If you are not yet using Vir.IT eXplorer PRO, it is advisable to install Vir.IT eXplorer Lite -FREE Edition- to supplement the antivirus in use to increase the security of your computers, PCs and SERVERS.
Vir.IT eXplorer Lite has the following special features:
- freely usable in both private and corporate environments with Engine+Signature updates without time limitation;
- fully interoperable with other AntiVirus software and/or Internet Security products (both free and commercial) already installed on your computer. It doesn't need any uninstallation and it doesn't cause slowdowns, as some features have been appropriately reduced to ensure interoperability with the AntiVirus software already on your PC/Server. This, however, allows cross-checking through the scan;
- it identifies and, in many cases, even removes most of the viruses/malware actually circulating or, alternatively, allows them to be sent to the C.R.A.M. Anti-Malware Research Center for further analysis to update Vir.It eXplorer PRO;
- through Intrusion Detection technology, also made available in the Lite version of Vir.IT eXplorer, the software is able to report any new-generation viruses/malware that have set in automatically and send the reported files to TG Soft's C.R.A.M
- Download Vir.IT eXplorer Lite from the official distribution page of TG Soft's website.
VirIT Mobile Security AntiMalware ITALIAN for ALL AndroidTM Devices
VirIT Mobile Security Italian Anti-Malware software that protects Android™ smartphones and tablets, from Malware intrusions and other unwanted threats, and empowers the user to safeguard their privacy with an advanced heuristic approach (Permission Analyzer).

TG Soft makes VirIT Mobile Security available for free by accessing the Google Play Store market (https://play.google.com/store/apps/details?id=it.tgsoft.virit) from which you can download the Lite version, which can be freely used in both private and corporate settings.
You can upgrade to the PRO version by purchasing it directly from our website=> click here to order
Acknowledgements
TG Soft's Anti-Malware Research Center would like to thank all users, customers, reseller technicians, and all people who have transmitted/reported material attributable to Phishing activities to our Research Center, that allowed us to make this information as complete as possible.
How to submit suspicious emails for analysis as possible phishing but also virus/malware or Crypto-Malware
You can submit materials to TG Soft's Anti-Malware Research Center safely and free of charge in two ways:
- any suspect email can be sent directly by the recipient's e-mail, to the following mail lite@virit.com,choosing as sending mode "Forward as Attachment" and inserting in the subject section "Possible phishing page to verify" rather than "Possible Malware to verify";
- save the e-mail to be sent to TG Soft's C.R.A.M. for analysis as an external file to the e-mail program used. The resulting file must be sent by uploading it from the page Send Suspicious Files (http://www.tgsoft.it/italy/file_sospetti.asp). Obviously if you want a feedback on the analysis of the data submitted, you have to indicate an e-mail address and a brief description of the reason for the submission (for example: possiible / probable phishing; possible / probable malware or other).
 For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis
For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis
We provide all this information to help you prevent credential theft, viruses/malware or, even worse, next-generation Ransomware / Crypto-Malware.
TG Soft's C.R.A.M. (Anti-Malware Research Center)


 The purpose is clearly to get the user to click on the provided link, which redirects to a web page designed, as always, to obtain the customer's sensitive data.
The purpose is clearly to get the user to click on the provided link, which redirects to a web page designed, as always, to obtain the customer's sensitive data. 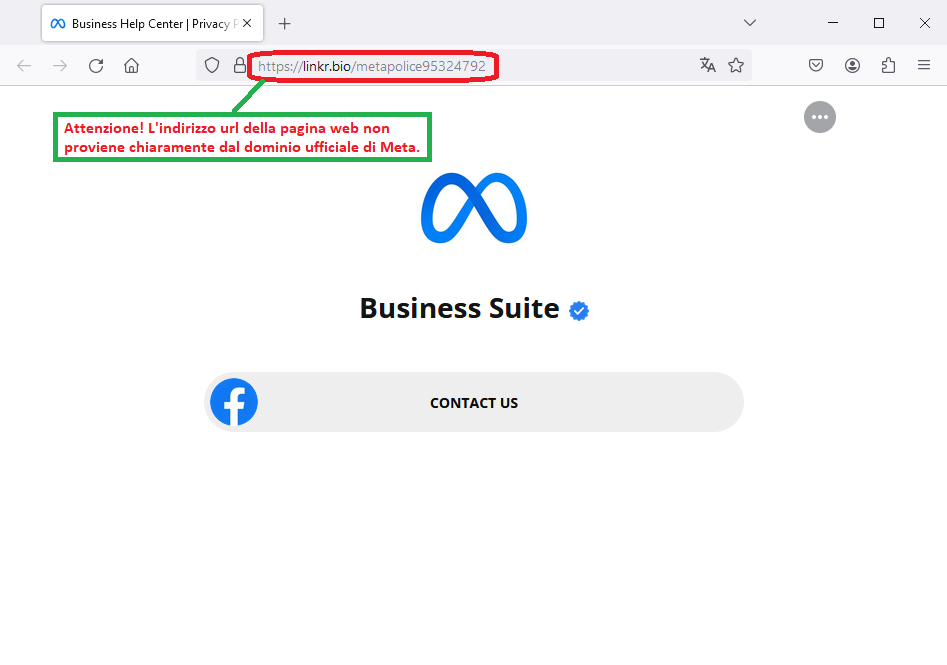 The purpose is clearly to lead the user to click on the proposed link, which redirects to a web page designed to steal the user's sensitive data.
The purpose is clearly to lead the user to click on the proposed link, which redirects to a web page designed to steal the user's sensitive data.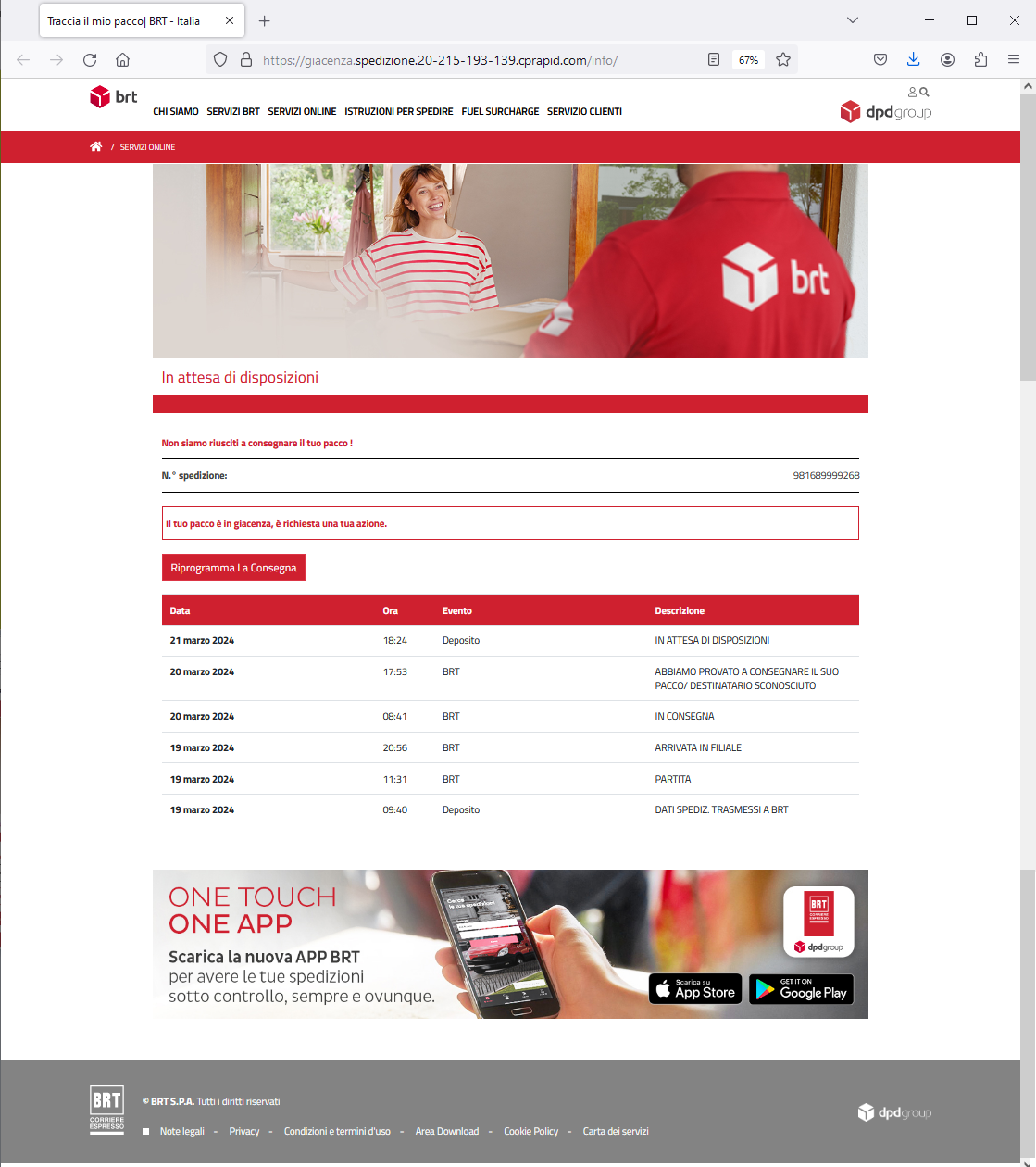 The purpose is clearly to lead the user to click on the proposed link, which redirects to a web page that, as always, requires the entry of the user's sensitive data in order to steal them.
The purpose is clearly to lead the user to click on the proposed link, which redirects to a web page that, as always, requires the entry of the user's sensitive data in order to steal them.
 For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis
For more details on how to safely forward suspicious e-mails, we invite you to consult the following public page: How to send suspicious emails for analysis